Better responses with workflows that reason
Intelligent response that your team can trust
Exabot Respond turns triage into consistent, auditable actions. AI reasoning nodes analyze context to build agents that automate busywork, enforce policies, verify with users, execute containment, and adapt safely with guardrails, approval gates, and full audit trails.
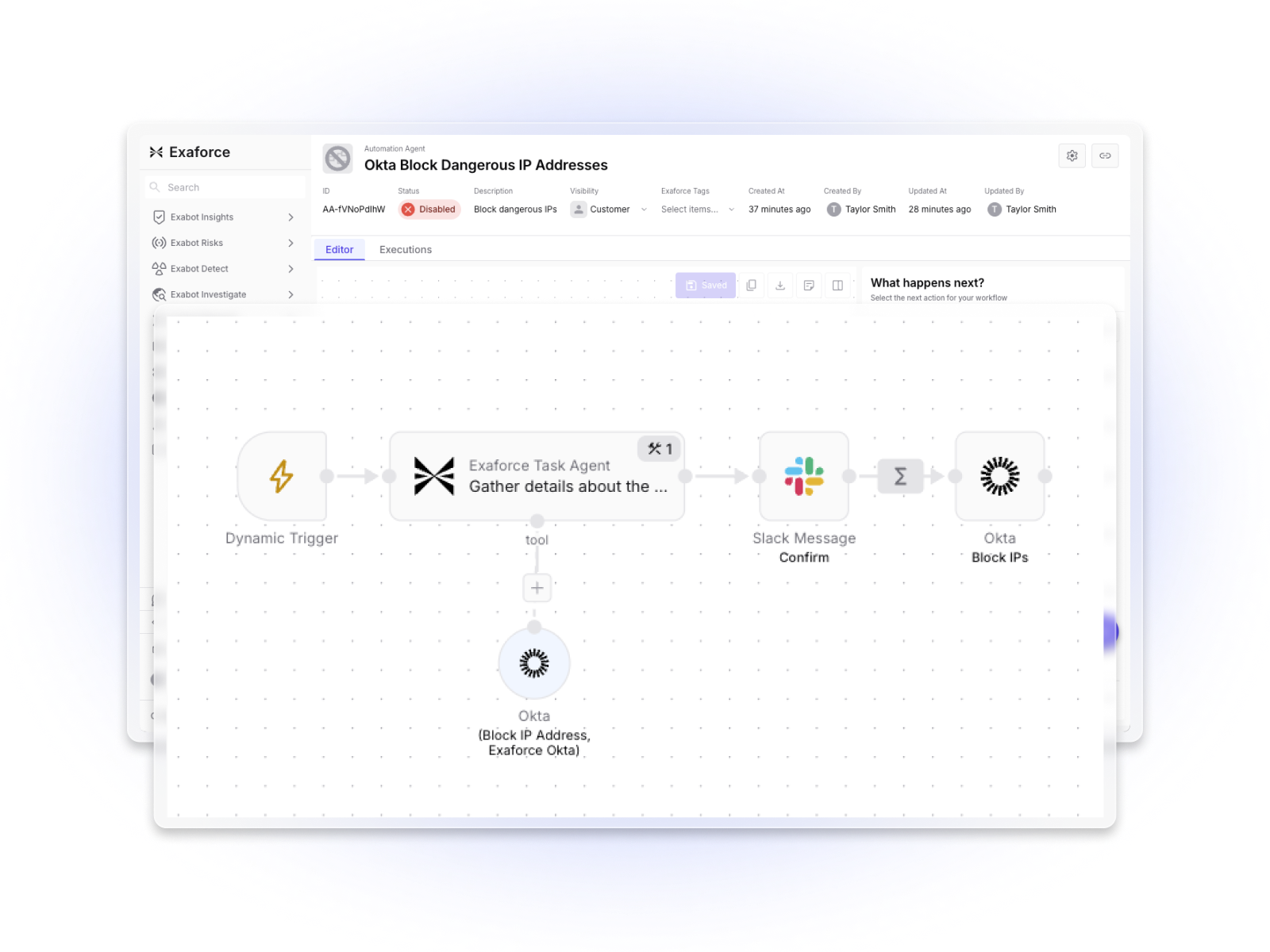
Build workflows that adapt and reason
Go beyond rigid SOAR playbooks with AI agents that make intelligent decisions within your workflows. Automation Agents combine deterministic logic with AI-powered reasoning nodes that analyze context from our semantic and behavioral models, extract data from connected sources, connect identities, evaluate conditions, and recommend appropriate actions. This makes workflow creation faster and response outcomes smarter without complex scripting.
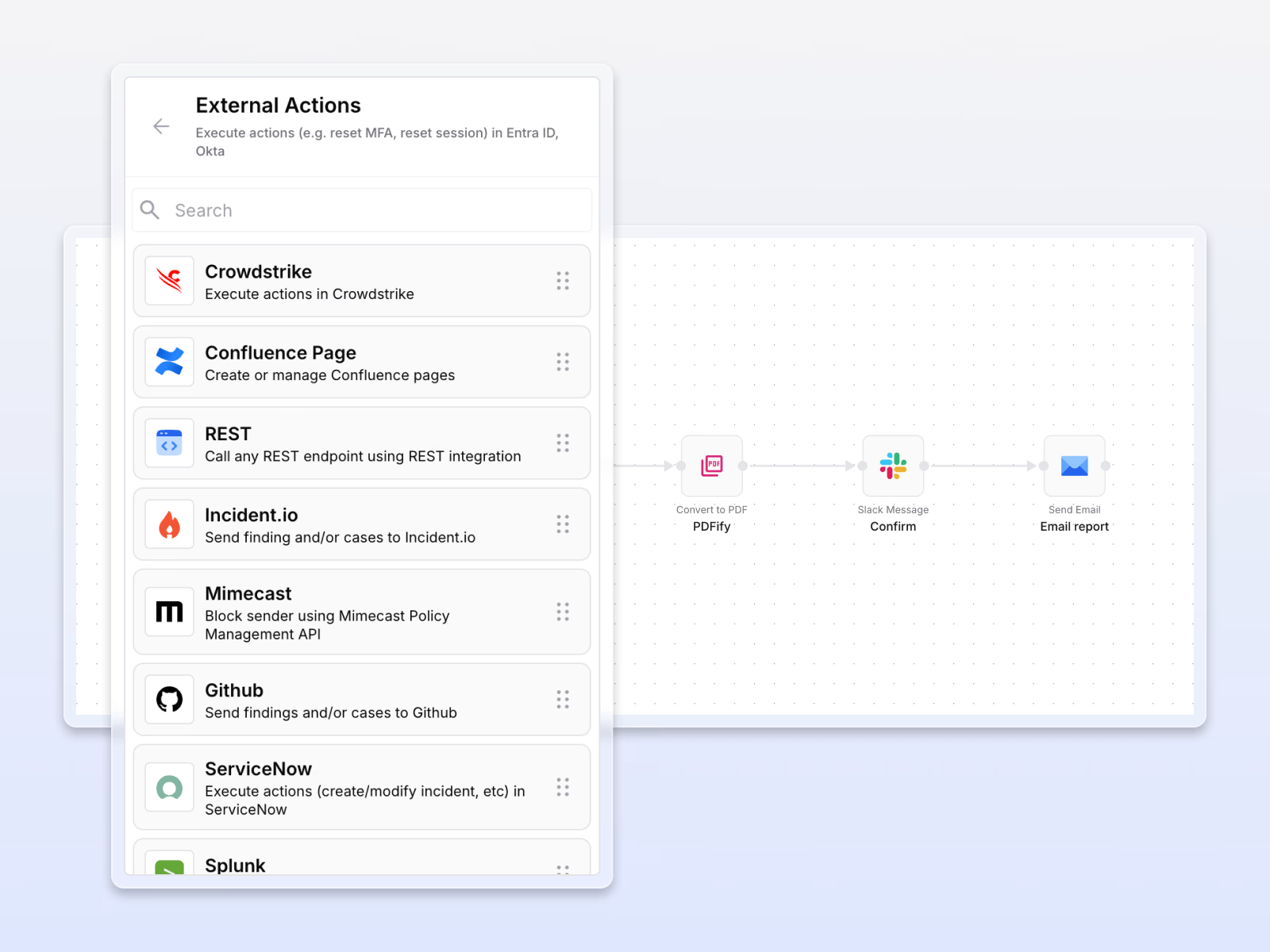
Leverage powerful tools and integrations
Automation Agents use a comprehensive toolkit to gather intelligence and take action. They can search the web via Perplexity for real-time context, validate IPs and domains with reputation services, enrich IOCs from threat intel feeds, call third-party REST APIs and webhooks, and interact with connected platforms. Agents orchestrate these tools to combine evidence from multiple sources, add external context, and execute coordinated responses.


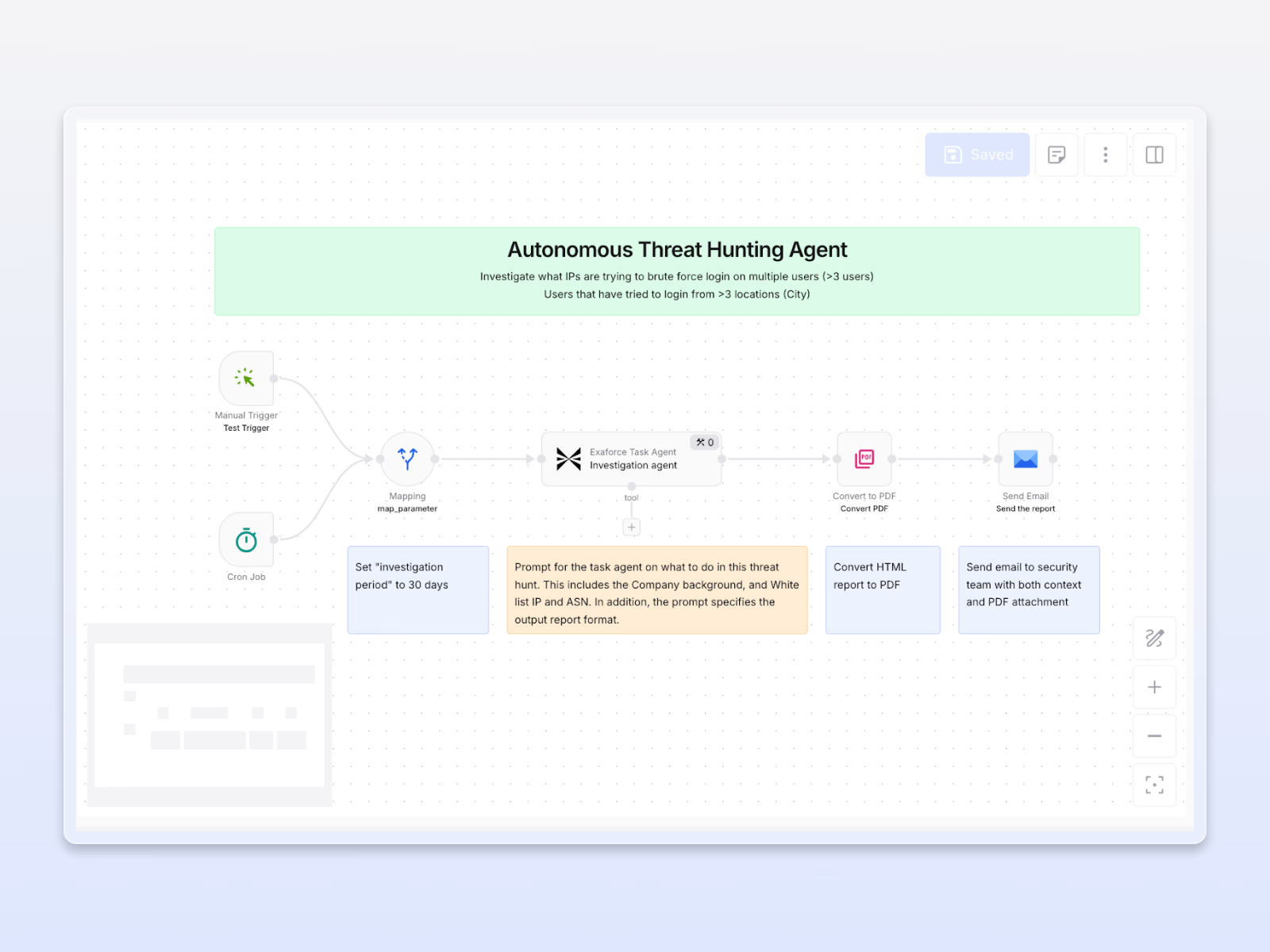
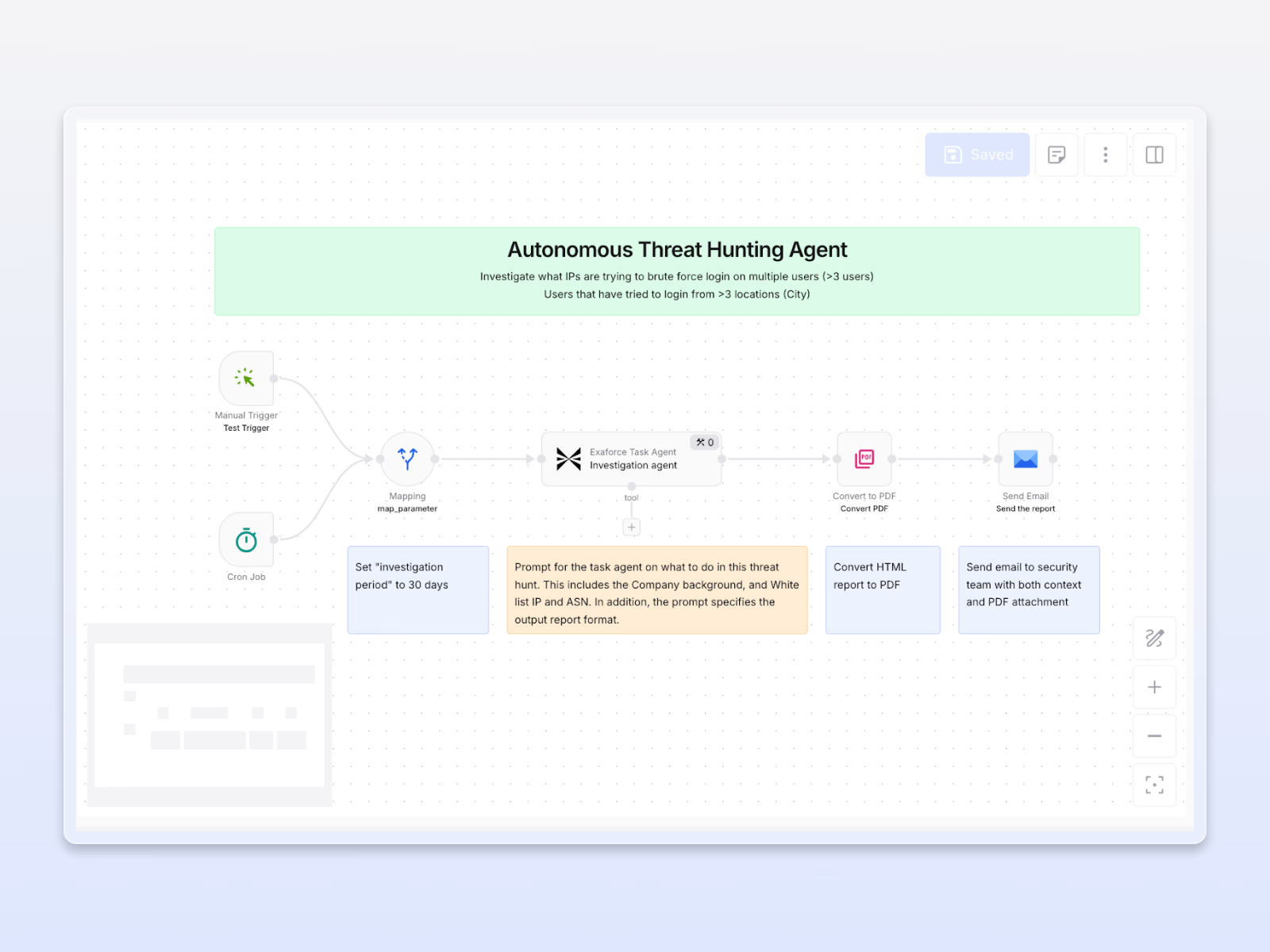
Schedule automated threat hunting
Because Exabots have visibility into your full environment, including connected identities, cloud activity, SaaS behavior, and endpoints, you can build agents that go looking for threats before alerts fire. Ask a hypothesis in plain English, and the agent queries across your infrastructure and returns findings. Run it on a schedule, trigger it after an incident, or wire it into an ongoing monitoring workflow.
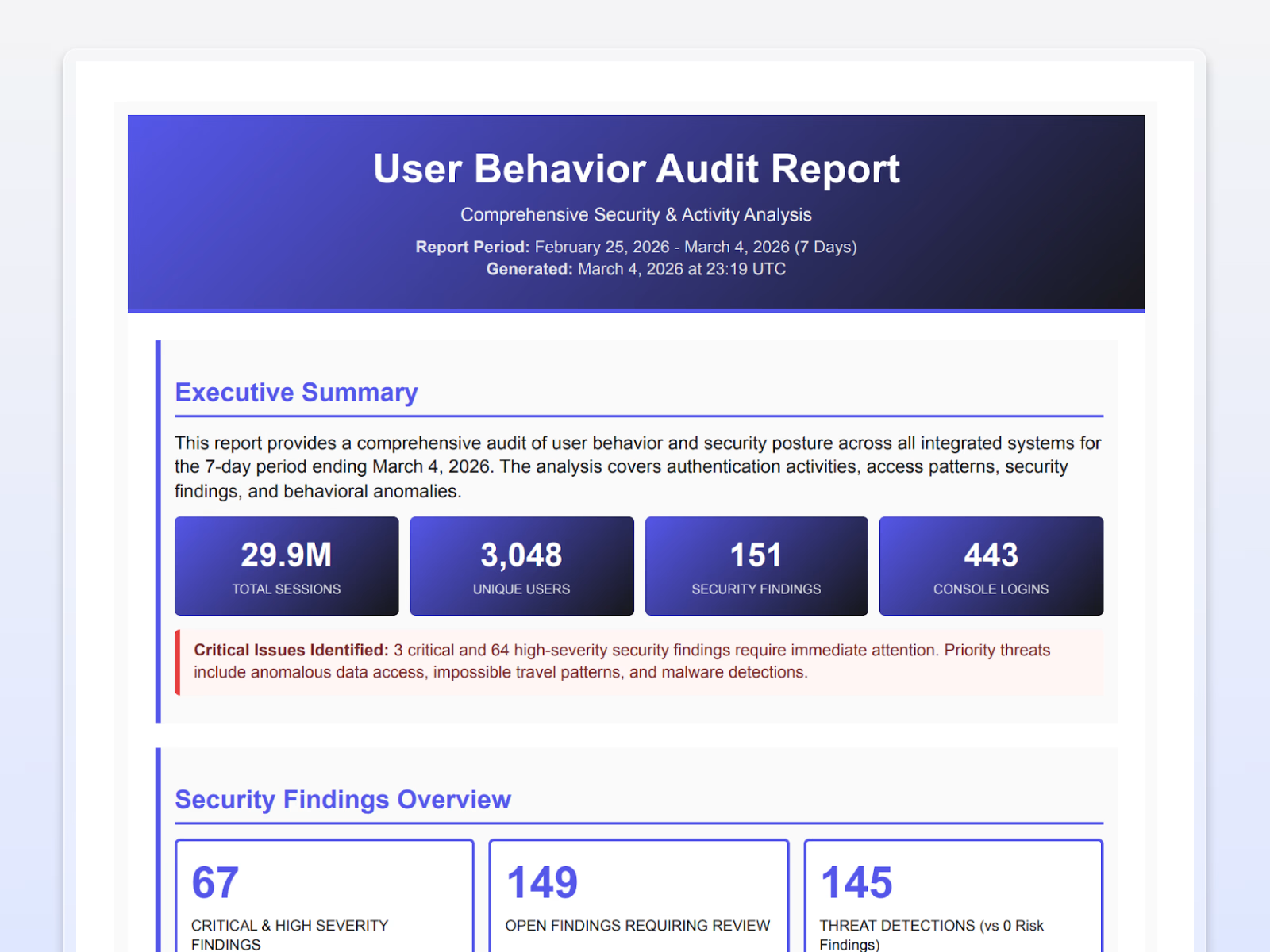
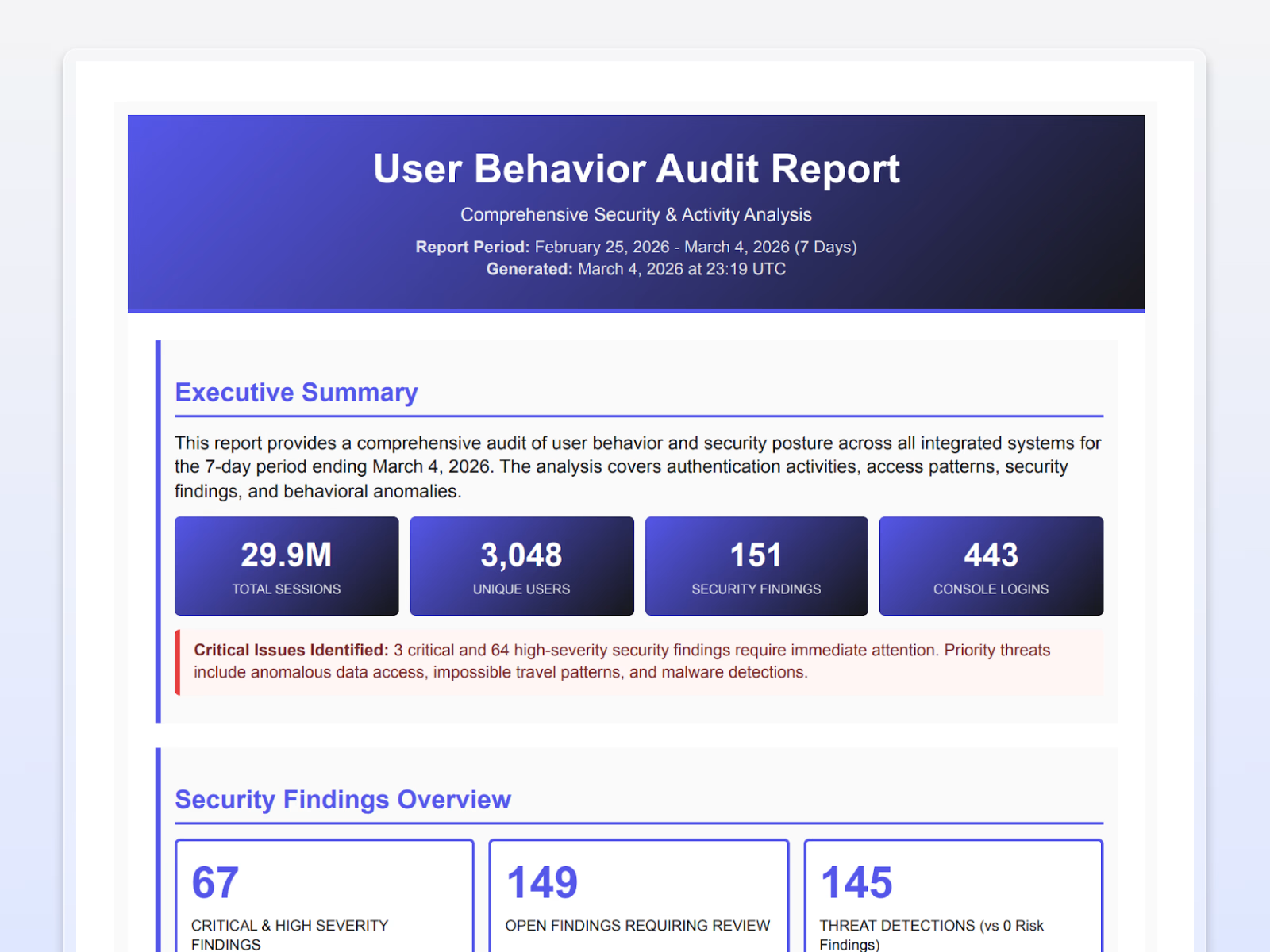
Automate custom reporting
Eliminate hours of manual reporting with agents that gather evidence across the platform, analyze findings and trends, and generate tailored, audit-ready reports for compliance, post-incident reviews, executive briefings, and threat summaries.
Contain threats before they escalate
Take decisive action to stop threats in their tracks. Isolate cloud instances, quarantine or delete malicious emails, block IPs, disable endpoints, reset MFA or passwords, suspend users, and revoke sessions across Okta, Entra ID, AWS, email platforms, and more. Built-in guardrails ensure every response is secure, approved, and reversible.


Featured response capabilities
Purpose‑built to accelerate containment while minimizing risk.
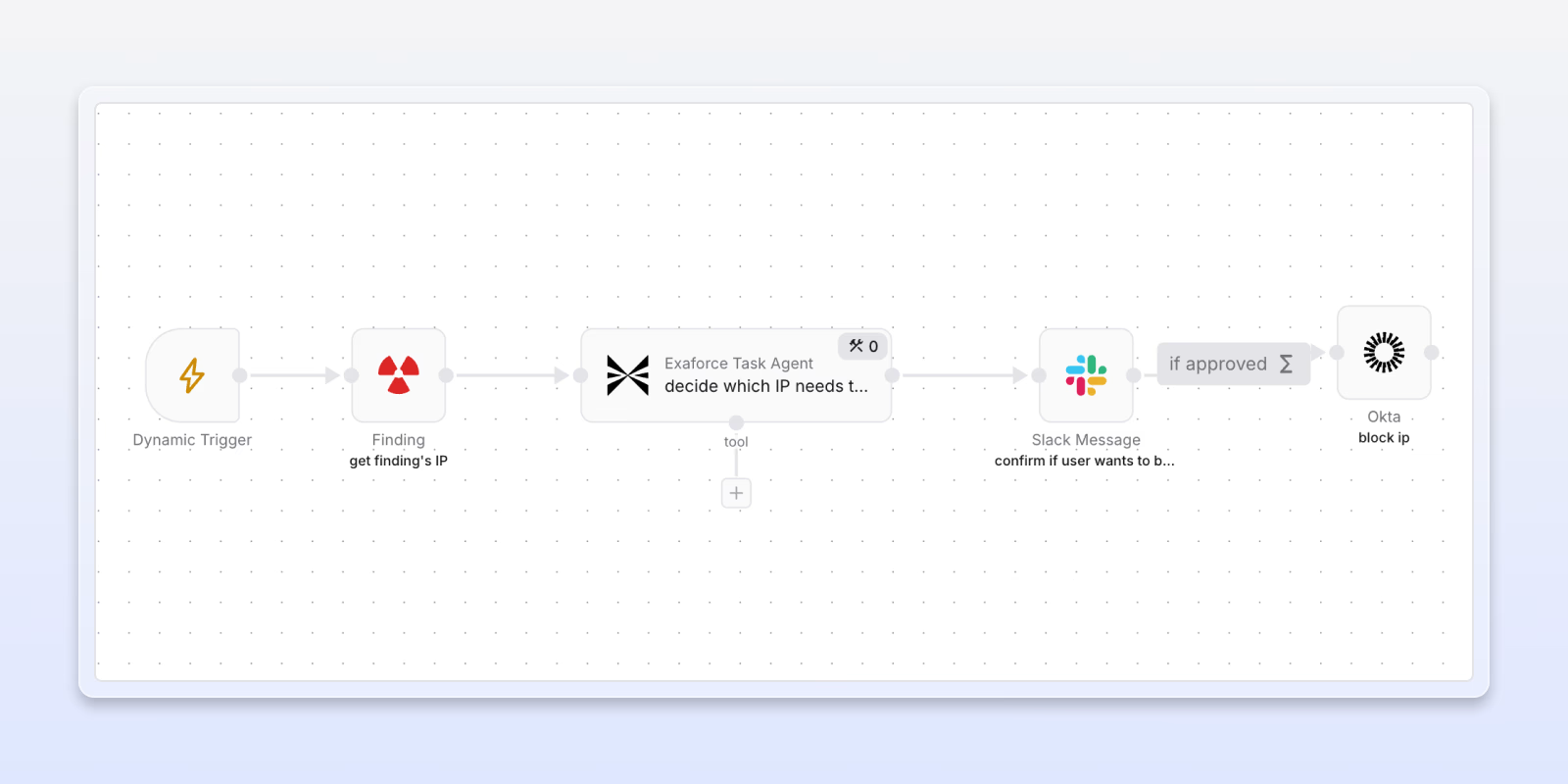
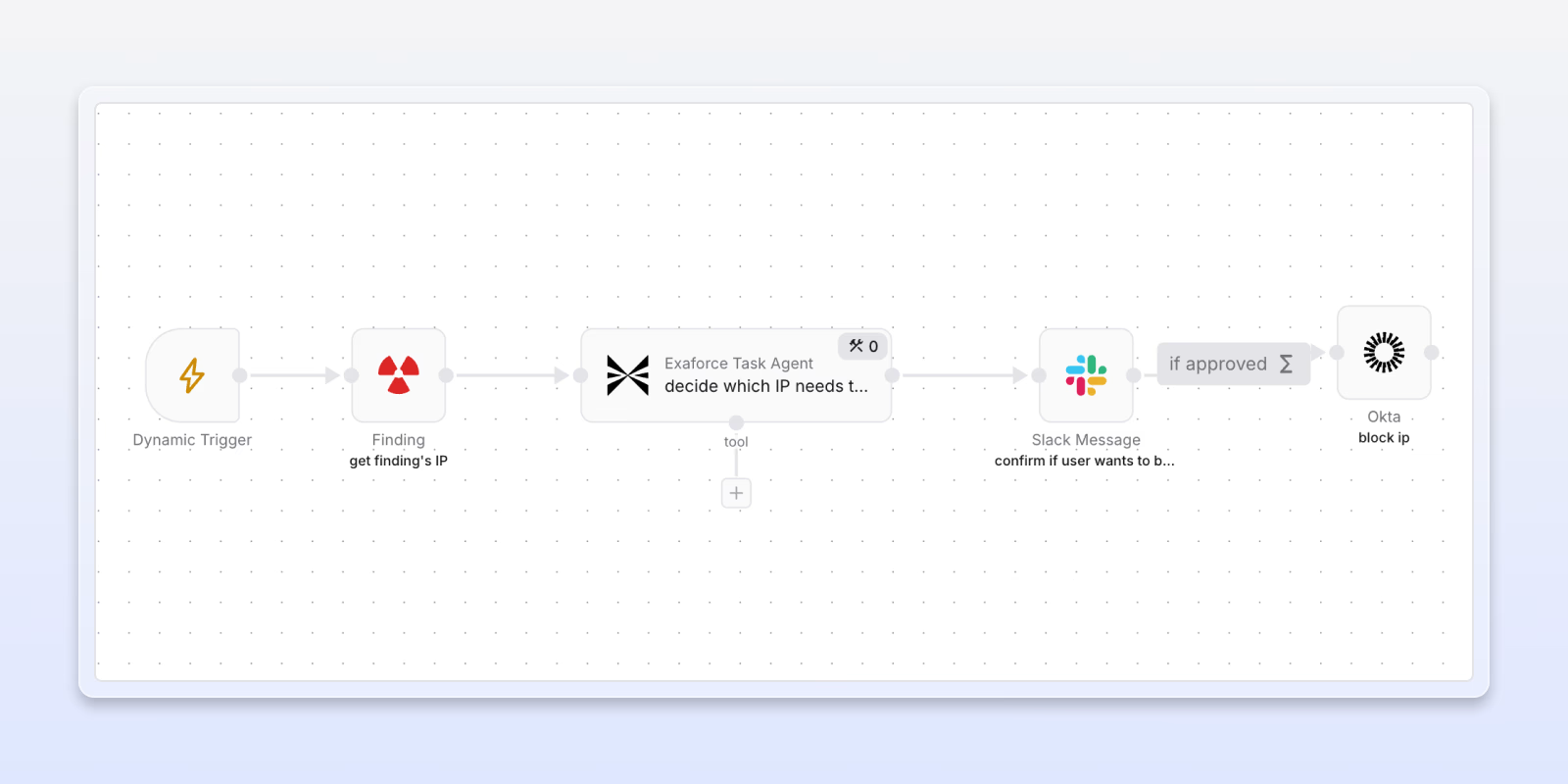
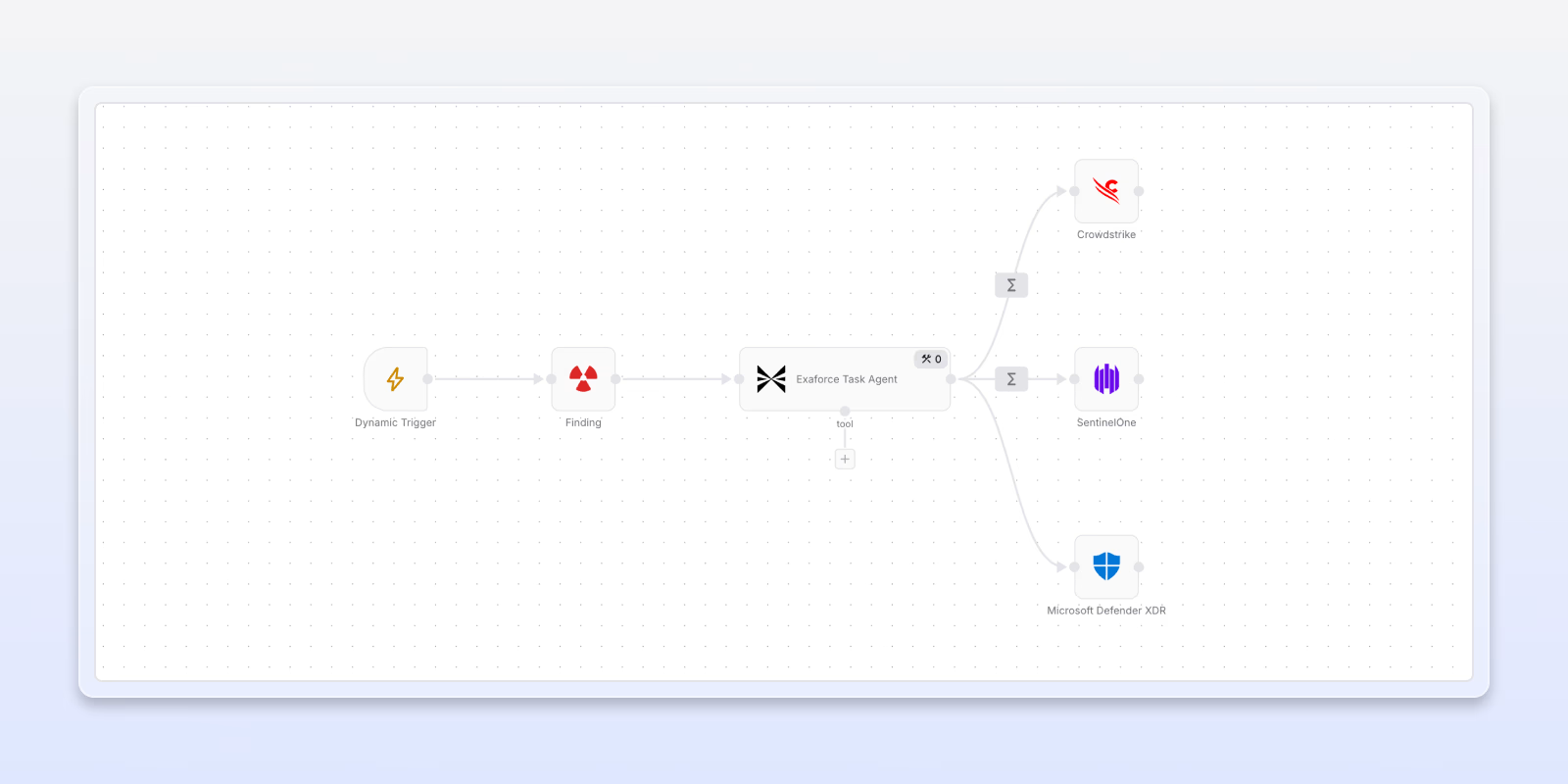
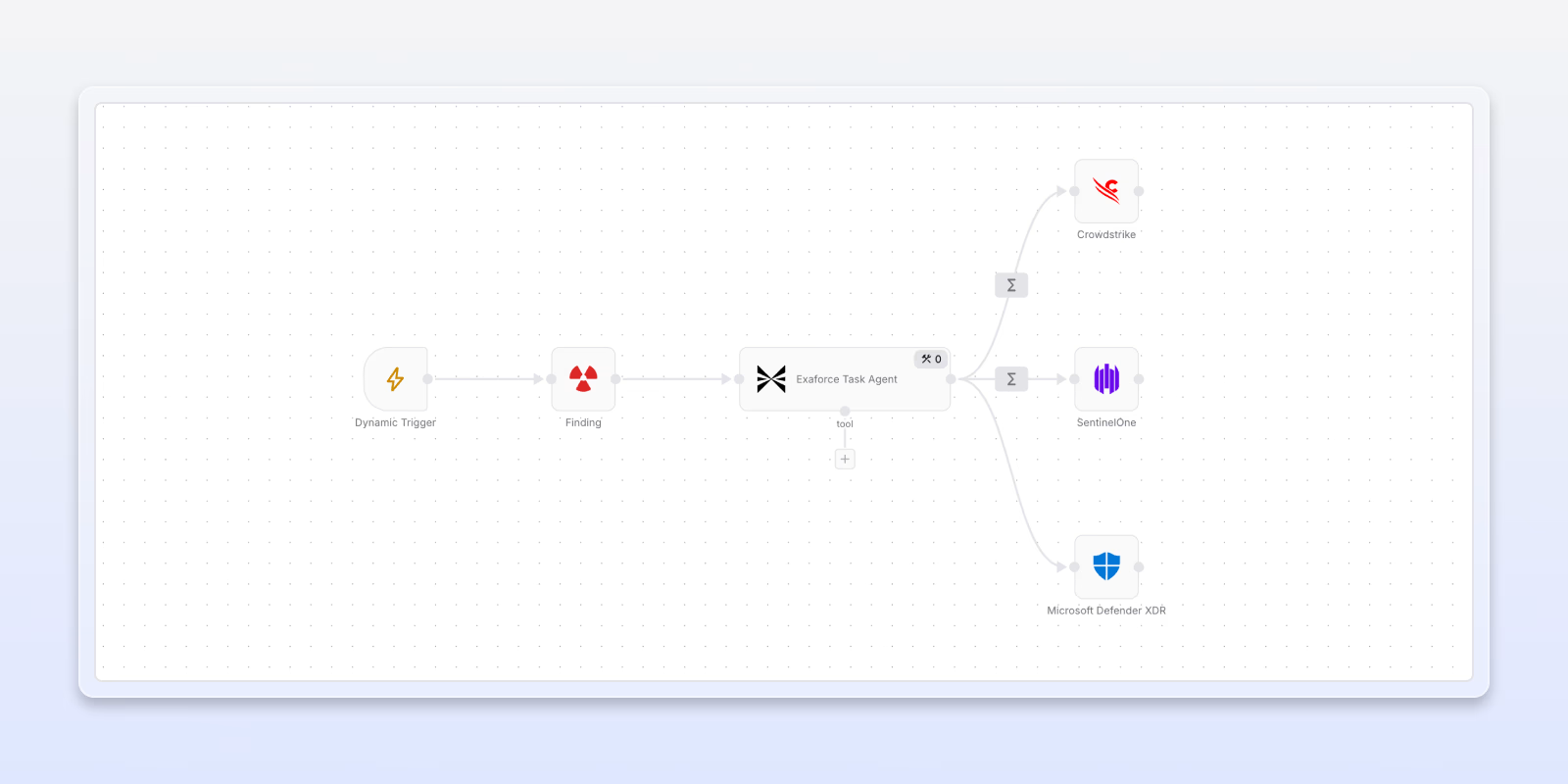
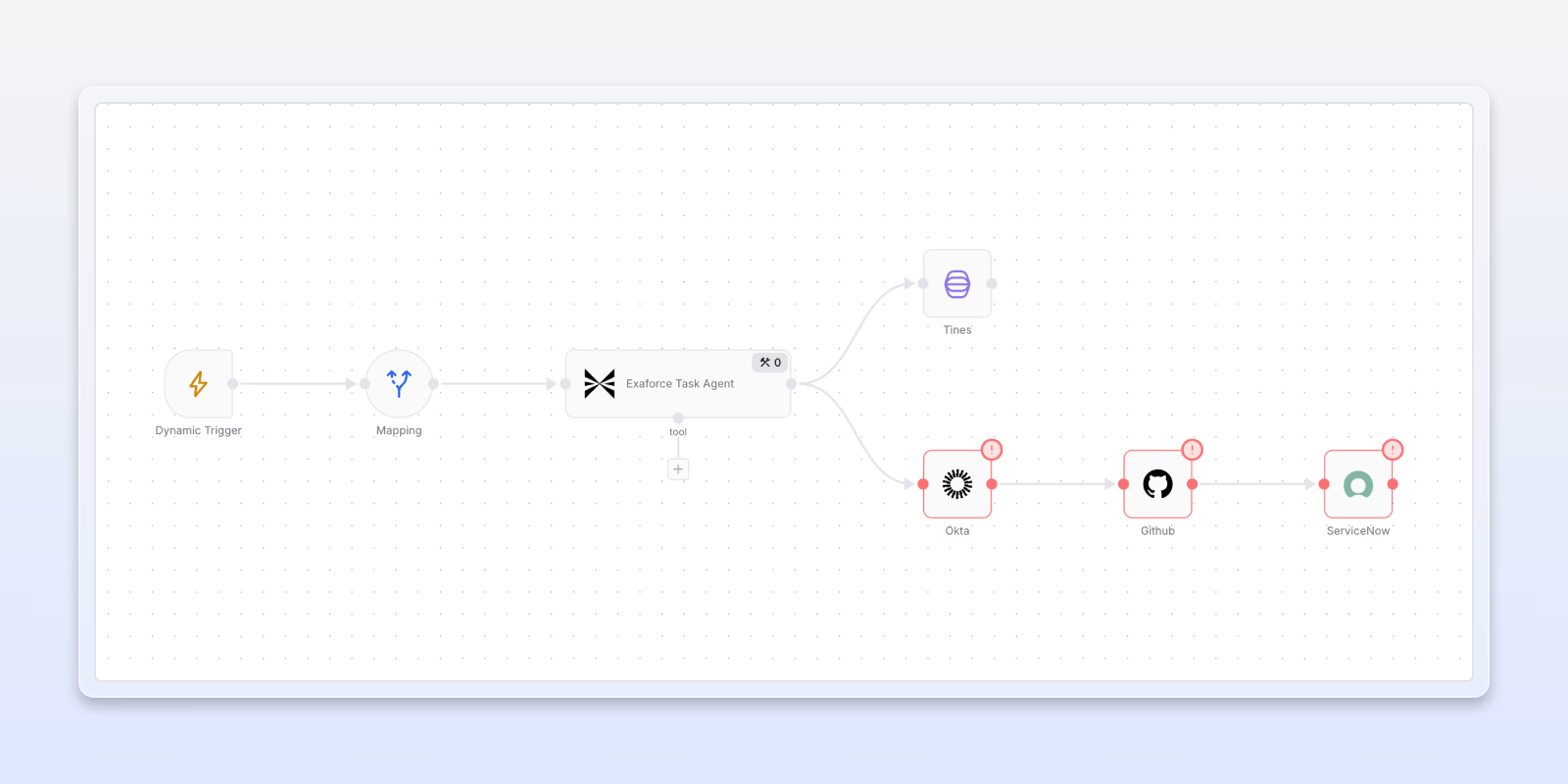
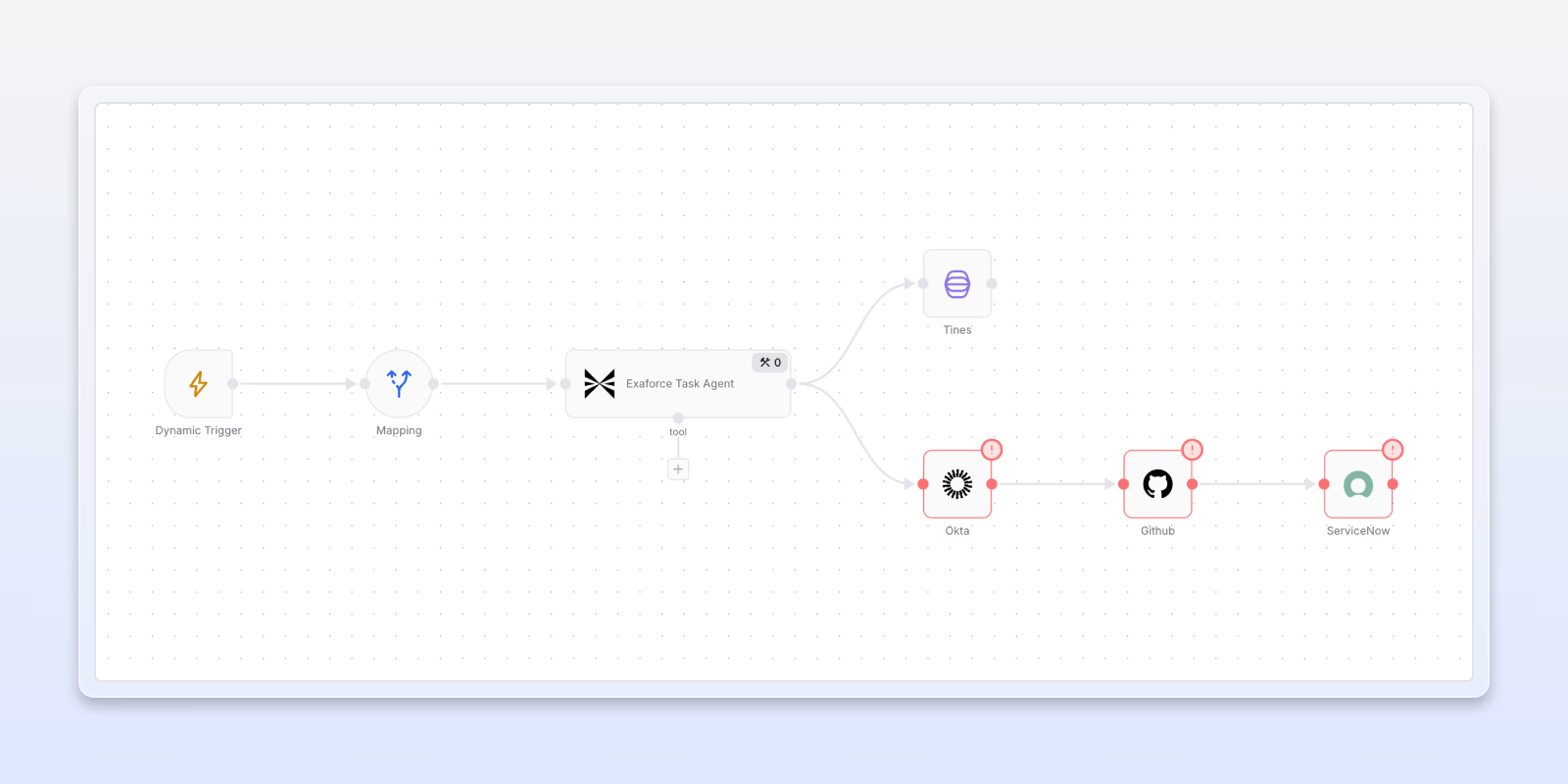
Automation workflows
Visual workflow editor to build custom workflows with deterministic and agentic steps.
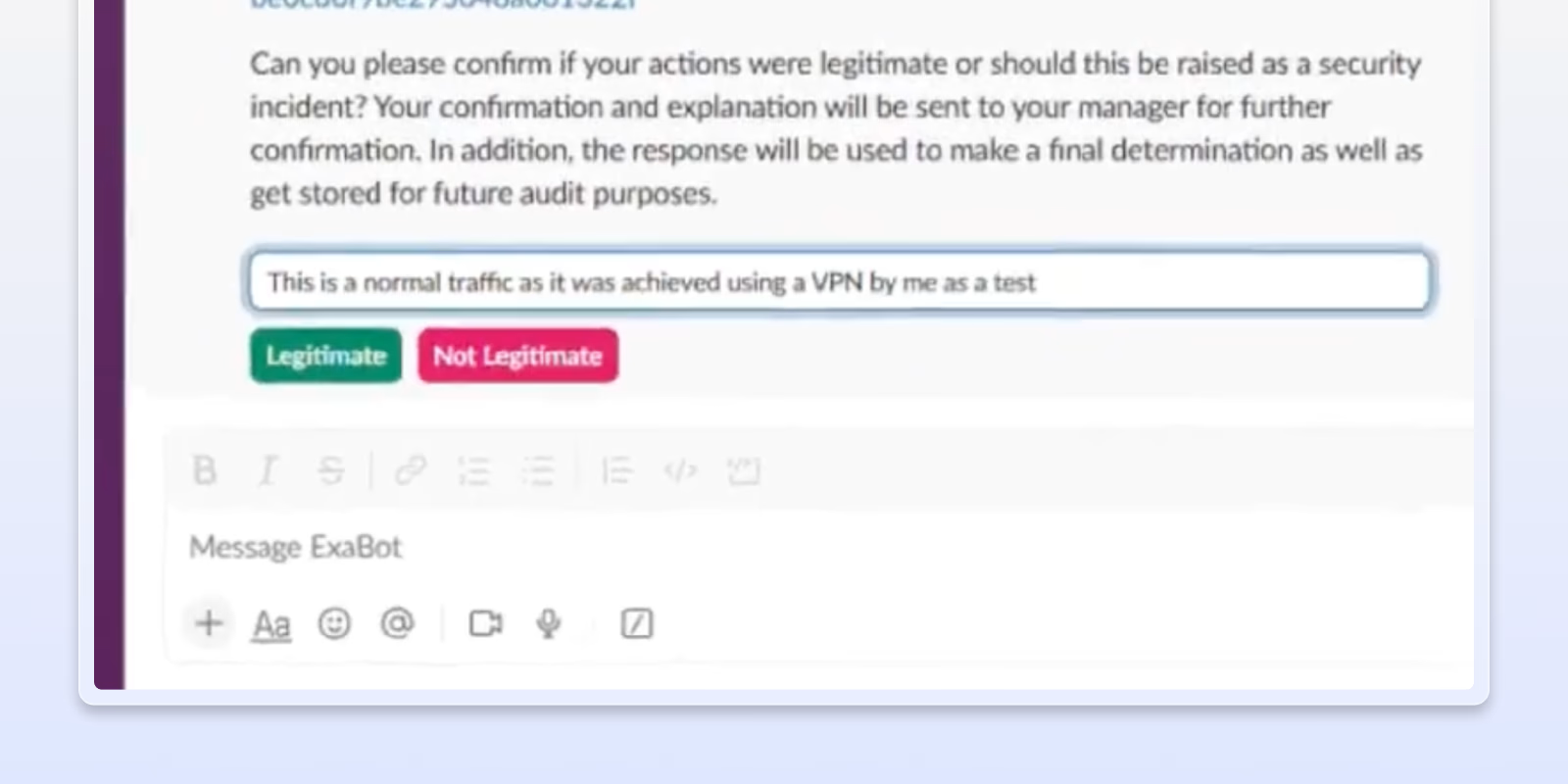
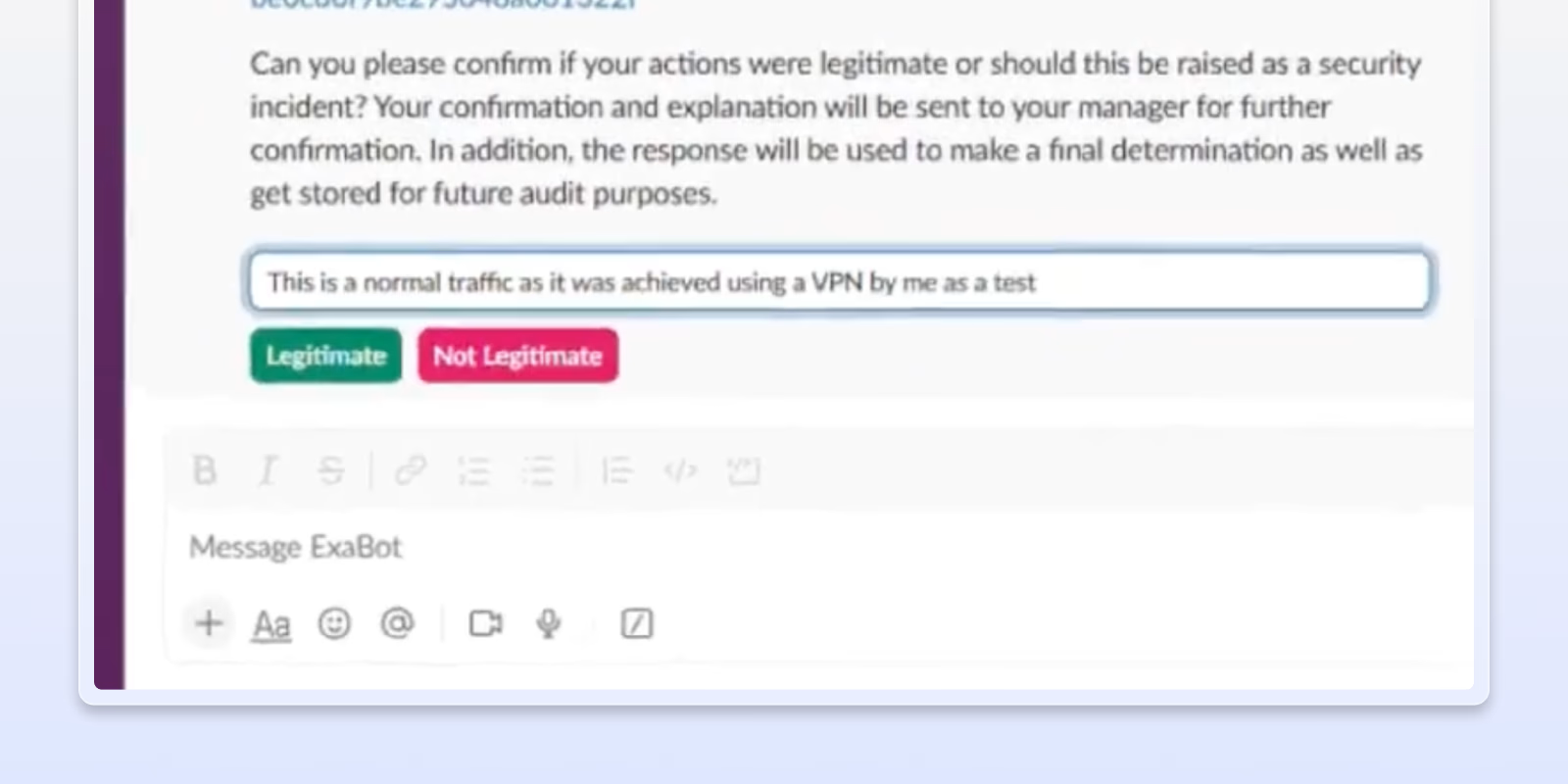
Slack confirmations
OOTB prompts for user and manager validation with buttons, timeouts, and auto‑escalation.
Trigger endpoint actions
Quarantine affected endpoints and enrich alerts in real time with up-to-date device context to accelerate investigation and response.
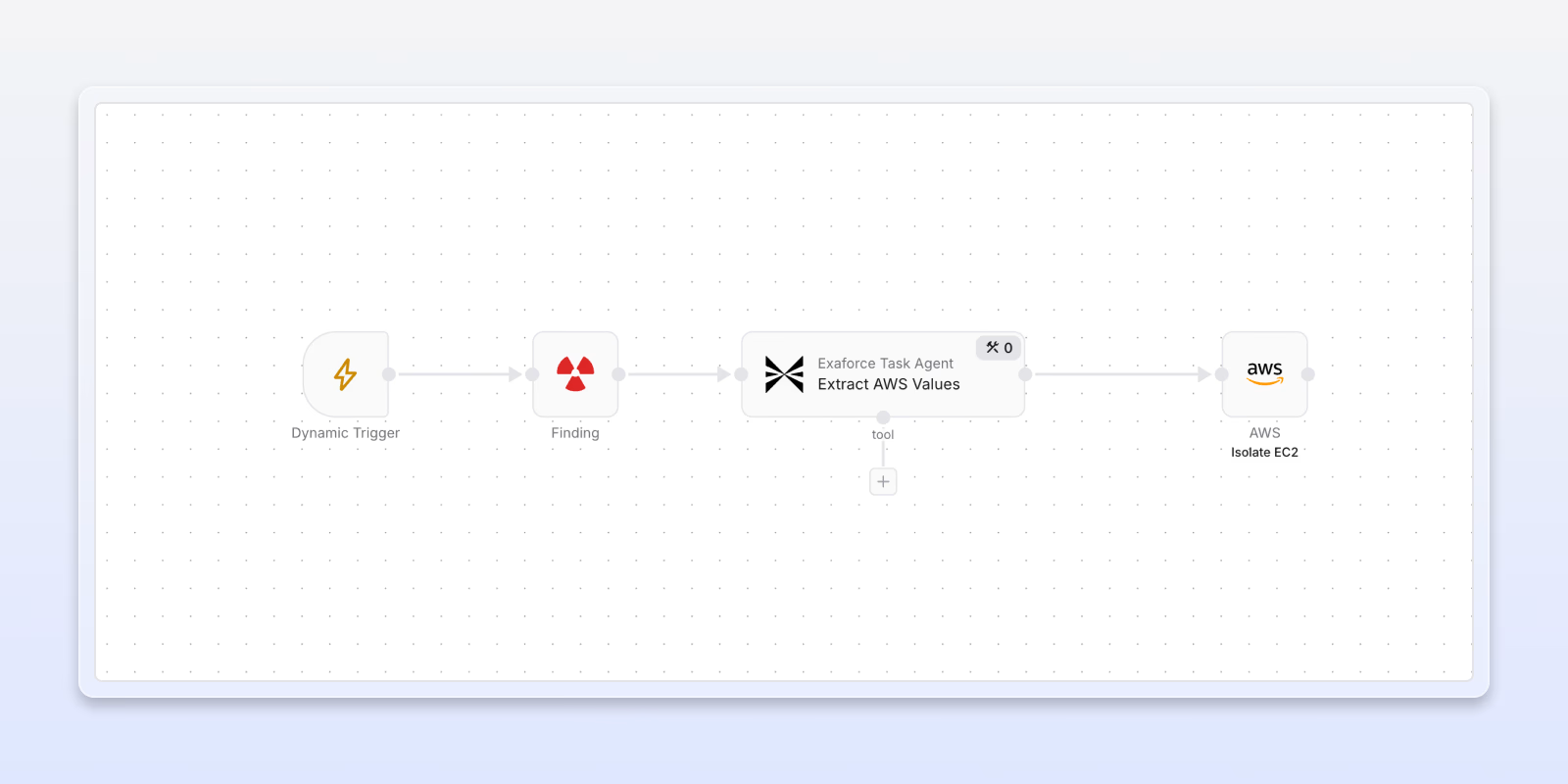
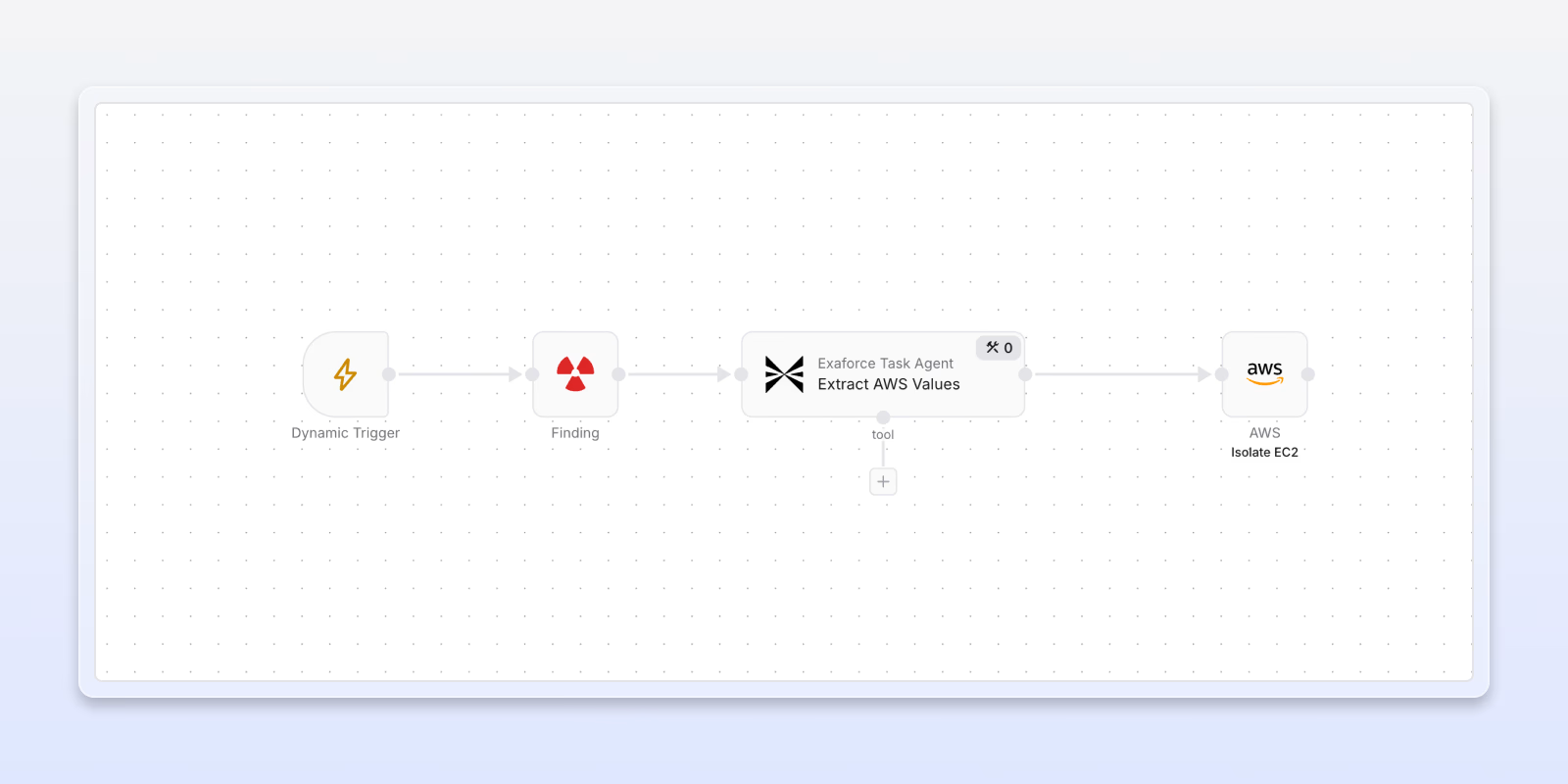
Trigger IaaS actions
Isolate affected instances or hosts, disable compromised users, and update security groups to contain IaaS threats.
Trigger SaaS actions
Reset users, revoke access, automatically create service tickets, and more SaaS response actions to contain and remediate incidents.
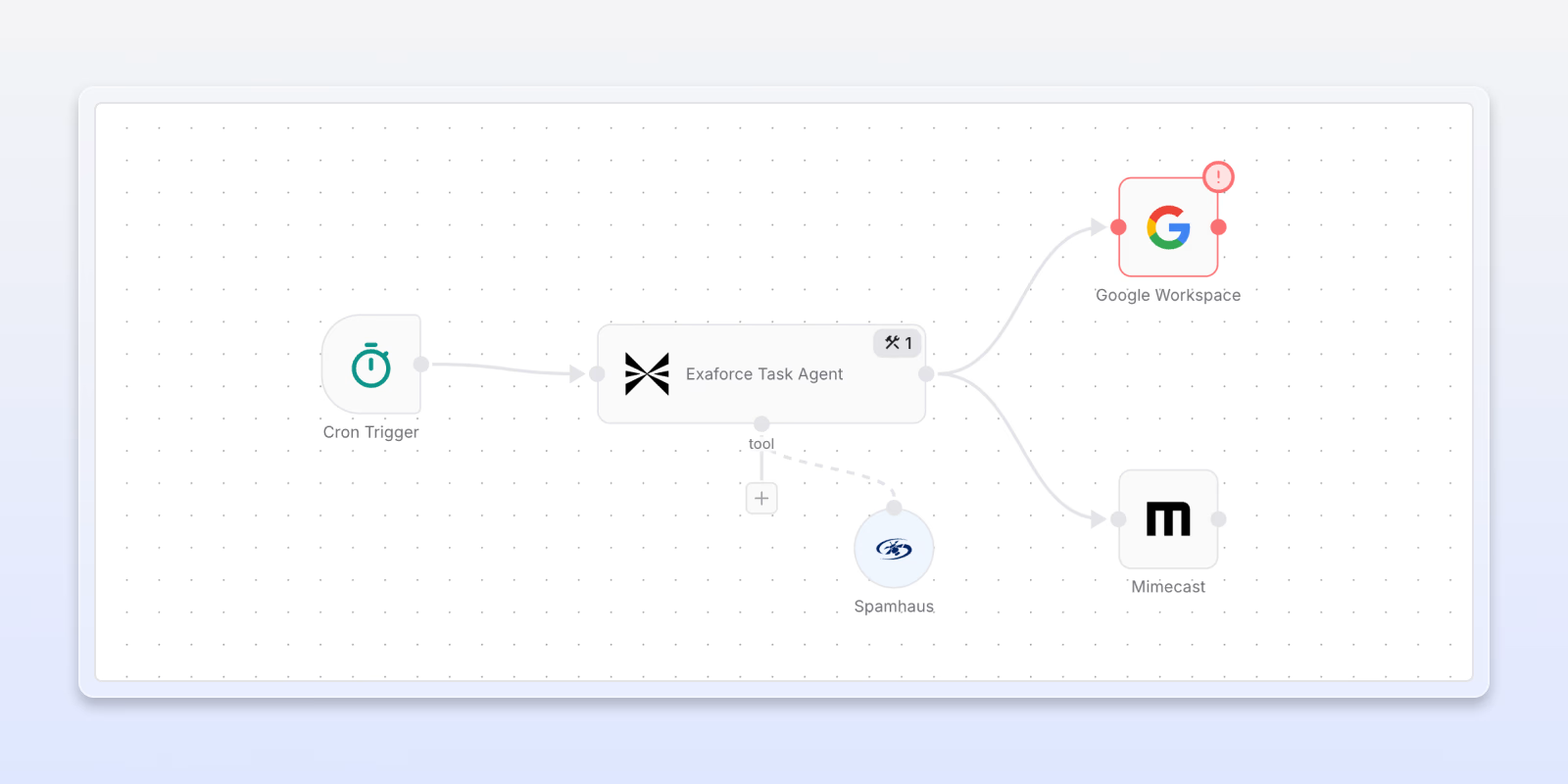
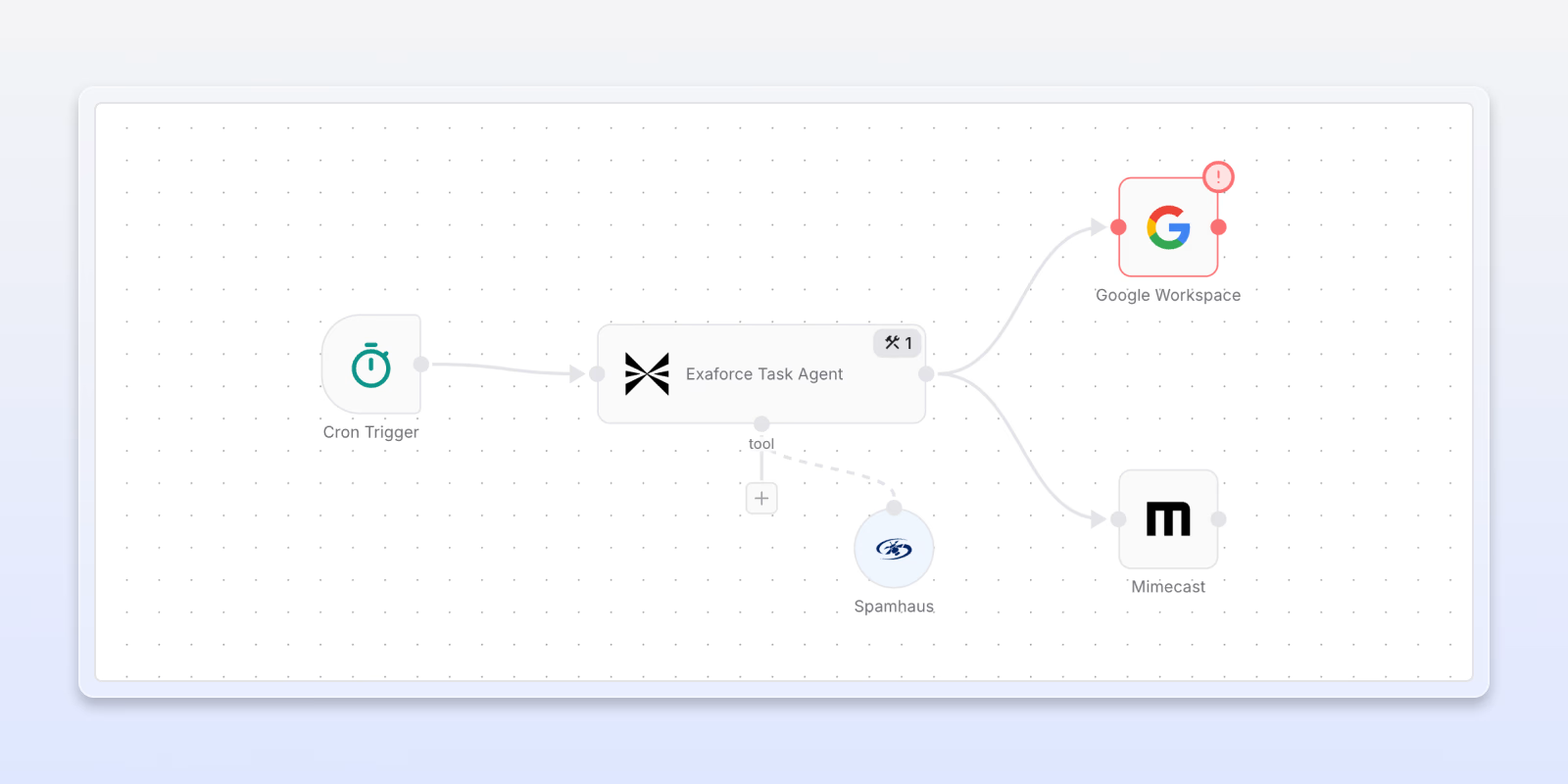
Trigger email actions
Quarantine or delete malicious emails, validate whether an IP or sender is spam or dangerous, and take additional response actions to stop email threats.

Exaforce has significantly strengthened our GitHub detection and response. Following our recent credential breach, their platform enabled us to quickly pinpoint and neutralize threats, ensuring our code repositories are far better protected.