When a cyberattack lands, the real question that needs answering right away is how far the damage can spread. Security blast radius is the framework that answers that question, and for teams managing sprawling cloud and hybrid environments, it's one of the more practical ways to think about risk.
If your organization experienced a breach tomorrow, could you say with confidence how far an attacker could move before running into a wall? Most security leaders, if they're being straight with themselves, can't.
Note on terminology: In mid-2024, a critical vulnerability in the RADIUS network authentication protocol was disclosed and named "Blast-RADIUS." This article focuses on the broader cybersecurity concept of blast radius as a risk framework. For details on the protocol vulnerability, see the CVE-2024-3596 disclosure on NIST NVD.
What is a security blast radius?
In cybersecurity, blast radius refers to the total scope of damage that could result from a single security incident. It describes how far an attacker can move, how many systems they can access, and how much data they can exfiltrate after gaining an initial foothold.
The term borrows from the physical concept of an explosion, where the epicenter is the point of compromise (a phished credential, an exploited vulnerability, a misconfigured cloud storage bucket), and the blast radius is how far the destructive force reaches from that point.
A narrow blast radius means an attacker who compromises one account or endpoint can only access a small, isolated slice of your environment. A wide blast radius means that the same initial compromise can cascade across your network, your cloud workloads, your identity infrastructure, and your data, leading to the kind of breaches that make headlines.
Blast radius vs. attack surface: what's the difference?
These terms are often conflated, but they measure different things. Your attack surface is the total set of entry points an attacker could target, such as exposed ports, internet-facing services, employee credentials, and third-party integrations. It's a measure of opportunity before an attack occurs.
Your blast radius is a measure of consequence after a successful compromise. It answers the question of, given that an attacker got in here, how bad can it get?
Reducing your attack surface limits how attackers can enter. Reducing your blast radius limits how much harm they can do once they're inside. Both matter, but blast radius is arguably more important for organizations that have accepted the reality that some attacks will succeed.
How to measure security blast radius
Measuring blast radius isn't an exact science, but security architects have developed practical frameworks for estimating it. One common approach considers three factors:
Asset Value × Exposure × Lateral Movement Potential = Estimated Blast Radius
- Asset Value captures how sensitive or critical an asset is. A database containing customer PII has a higher value than a dev workstation. Tier-zero assets like domain controllers, Active Directory ACLs, and certificate authorities sit at the extreme end.
- Exposure reflects how accessible an asset is. Is it behind a firewall? Is it directly reachable from the internet? Is it accessible to a large portion of your workforce?
- Lateral movement potential describes how easily an attacker who reaches one asset can pivot to adjacent systems. Over-privileged accounts, flat network architectures, and misconfigured trust relationships all increase this factor.
The diagram below illustrates how a single compromised endpoint can expand its reach through lateral movement in an environment with insufficient segmentation:
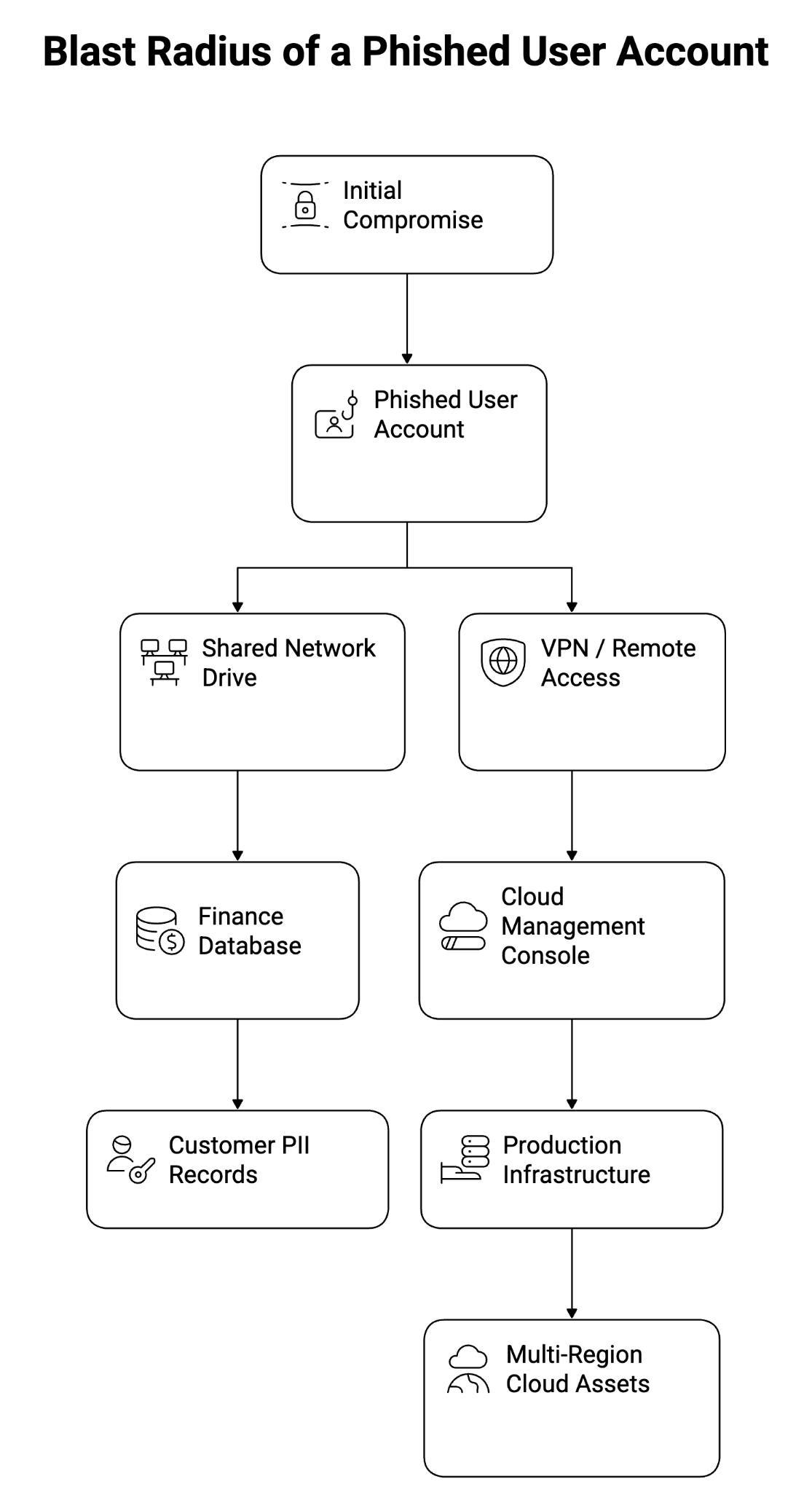
In a well-segmented environment, the compromise stays contained to the left side of this tree. In a flat network with over-privileged accounts, one phished credential can walk an attacker all the way to production cloud infrastructure.
The identity blast radius problem
Identity has become one of the most consequential dimensions of blast radius in modern environments. When a user account is over-privileged (and according to research from Tenable, this is true of a significant majority of accounts in enterprise environments), compromising it hands an attacker significant reach before they've done any lateral movement at all.
The concept of an identity blast radius captures the measure of what an attacker can access using only the permissions already granted to a legitimate account. In environments with poor access governance, a mid-level employee's credentials might grant read access to sensitive HR systems, write access to shared infrastructure repositories, and administrative rights to legacy applications that were never properly scoped.
Cloud environments amplify this risk. In AWS, GCP, and Azure, IAM misconfigurations routinely grant roles far more privileges than their function requires. The 2025 Verizon Data Breach Investigations Report found that credential abuse remains one of the leading initial access vectors, and cloud misconfigurations continue to expand what attackers can do with those stolen credentials.
Multi-account cloud architectures, when implemented correctly, can dramatically reduce identity blast radius by enforcing account-level isolation. When they're flat, a single compromised cloud IAM role can grant access to resources across regions and services.
Five strategies to reduce your blast radius
Understanding blast radius matters most when it changes how you design and operate your security environment. Here are the most effective controls security teams deploy to limit damage from any given compromise:
1. Apply the Principle of Least Privilege rigorously
Every user, service account, and application should have the minimum access required to perform its function. Nothing more. This sounds obvious, but in practice, privilege creep is nearly universal. Accounts accumulate permissions over time, roles get copy-pasted with excessive scope, and service accounts are granted admin rights "just in case."
Conducting regular access reviews and automating the detection of over-privileged accounts are foundational steps. The NIST guidelines on access control provide a useful framework for implementing PoLP at scale across both on-premises and cloud environments.
2. Segment your network
Flat networks are blast radius accelerants. Micro-segmentation creates logical boundaries within your environment so that a compromised workload in one segment cannot directly communicate with workloads in another without explicit policy permitting it.
Modern micro-segmentation goes beyond traditional VLANs to apply segmentation at the workload level, which means even within a cloud environment or data center, traffic between adjacent systems is controlled and logged. When evaluating your organization's detection and response capabilities, the presence or absence of network segmentation will significantly affect how quickly an attacker can reach high-value targets once inside.
3. Adopt a Zero Trust architecture
Zero Trust is the operational model best designed to constrain blast radius at a structural level. Rather than assuming that anything inside the network perimeter is trustworthy, Zero Trust requires continuous verification of identity, device posture, and context before granting access to any resource.
This shifts the security model from perimeter defense to perimeter-less, which matters enormously in cloud and remote-work environments where the traditional network boundary no longer exists. CISA's Zero Trust Maturity Model provides a practical roadmap for organizations at various stages of this transition.
4. Isolate cloud workloads and accounts
In cloud environments, account-level isolation is one of the most powerful blast radius controls available. Separating production, development, staging, and sensitive data workloads into distinct cloud accounts, with strict cross-account access policies, means that a compromise in one environment cannot automatically expand into another.
This is particularly important for organizations running AI-driven security operations that process sensitive log data and telemetry. If the systems that ingest and analyze security data live in the same blast radius as the infrastructure they're protecting, a sophisticated attacker can blind the SOC by compromising both simultaneously.
5. Implement continuous monitoring and automated response
Reducing blast radius is about prevention and the speed of detection and containment. The longer an attacker operates inside your environment, the larger the effective blast radius becomes. Automated detection and response capabilities that can isolate a compromised endpoint or revoke a suspicious session within minutes dramatically limit the spread of an incident.
Blast radius in incident response planning
Blast radius thinking should be embedded in your architecture and your incident response planning. When you're modeling scenarios for tabletop exercises, the questions that matter are: if this system is compromised, what can an attacker reach from there? If this credential is stolen, what actions can it authorize?
Mapping your environment's blast radius profile before an incident helps prioritize which assets need the most aggressive controls, which accounts require the closest behavioral monitoring, and which containment actions should be automated rather than manual.
Impact and actions
Security blast radius is one of the most useful mental models available to security leaders trying to prioritize their investments and controls. It shifts the conversation from "how do we keep attackers out" to "what happens when they get in," a shift that reflects the operational reality of modern threat environments.
The organizations best positioned to contain incidents are those that have mapped their blast radius before a breach occurs, applied least privilege and segmentation consistently, and built automated containment capabilities that can act faster than any human analyst could. Reducing blast radius isn't a project you complete. It's a property of your environment that you continuously measure and improve.
If you're evaluating how well your current security operations can detect and contain lateral movement in real time, exploring what an agentic SOC approach can offer in terms of automated investigation and response is a practical next step.





