Threat hunting is one of the few security practices that is unapologetically proactive. The whole point is to go looking for attacker behavior that slipped past your detections, not to wait for an alert to beg for attention. The branding problem is that, in most environments, threat hunting is also slow, messy, and expensive. Until now, security teams have spent time basically getting better at search. Better SIEM queries, better detection rules, better dashboards, yet incident timelines still get stitched together the same way. An analyst opens a case, pivots across tools, manually collects evidence, writes down details, and asks a senior analyst for a second opinion. The cycle then repeats. With the shift to AI, the fundamentals remain the same, but the cumbersome parts of the workflow get a boost.
“Vibe hunting” is the new cool kid on the block.
If “vibe coding” is you expressing intent and letting AI do the mechanical work, vibe hunting is the same shift applied to threat hunting. You stop thinking in terms of “what query should I write” and start thinking “what story is happening in my environment, and what would I need to prove it.”
Vibe hunting is what happens when an AI SOC platform compresses the hunting process so dramatically that it stops feeling like a special event you schedule and starts feeling like something you can do whenever your instincts twitch. Not a quarterly initiative. Not a purple-team ritual. Just a fast, repeatable motion.
And yes, it’s so easy even the CISO can participate in a hunt
In this article, we’ll show how Blue Teamers can actually apply vibe hunting in detection, threat hunting, and incident response through a real-world case study on the Axios NPM supply chain attack. We’ll explore how it streamlines workflows, saves time, and improves outcomes, along with Exaforce’s approach to making it work in practice.
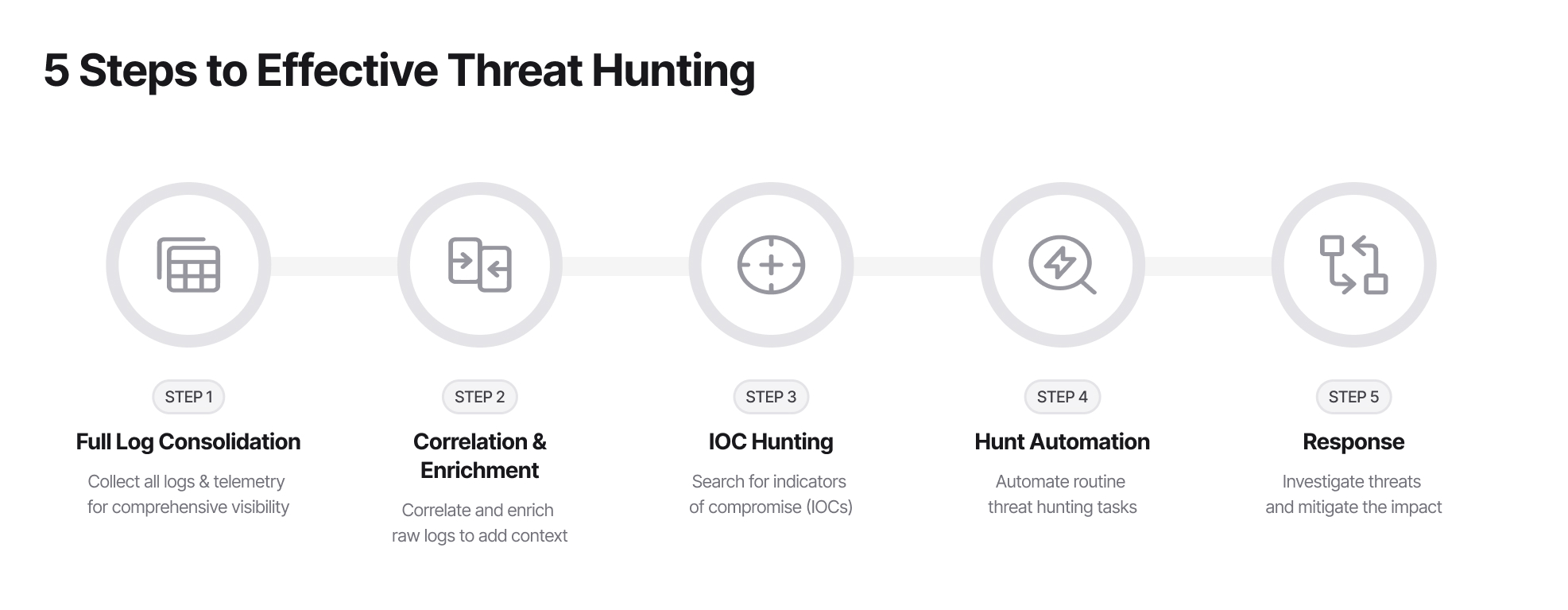
Threat Hunting in a Traditional World
Credible sources are pretty consistent in saying that threat hunting is supposed to be practitioner-led and hypothesis-driven. Forrester explicitly frames it as a “human-led exercise” and defines it as “a practitioner-led, hypothesis-driven exercise to find attacks that circumvent detection capabilities.” That is the ideal. The reality is that the “human-led” part often turns into “human-burdened,” because hunts typically require:
1. Log Consolidation
Effective hunting requires comprehensive telemetry. Ingest data across identity, endpoints, SaaS, cloud control planes, networks, email, and DNS to eliminate visibility gaps.
2. Correlation & Enrichment
Transform raw events into actionable intelligence. This involves normalizing fields, deduplicating data, and mapping actions to specific behaviors. Analysts must enrich indicators like IPs and hashes while stitching sessions together across disparate tools and schemas.
3. IOC Hunting
Search for Indicators of Compromise following new threat intelligence. Query your environment for specific entities such as file hashes, malicious domains, IP addresses, and process names to determine impact.
4. Hunt Automation
Use playbooks to automate predictable tasks like querying, artifact retrieval, and ticket creation. While automation accelerates data collection, human analysts remain necessary to interpret findings and identify relevant artifacts within a specific environmental context.
5. Response
Validate the blast radius and gather evidence for confirmed hits. Coordinate remediation efforts, such as isolating workloads or resetting credentials, to neutralize the threat.
The Rise of Vibe Hunting
LLM agents are beginning to change this dynamic in a meaningful way. Instead of a human painstakingly crafting the next query, debugging it, and reading through documentation, an agent can generate the query automatically, with the human only needing to tweak what is necessary. Yet even this approach faces the challenge of multiple systems generating events that still require manual pivoting. Even if a SIEM is configured to collect events from all user systems and services, a threat hunter still needs to move across multiple data sources, correlate them, and understand how an attacker moves through the environment.
LLM agents, without the right context, however, cannot autonomously stitch data with accuracy. In order to be really reliable, they need to be founded upon a strong foundation of knowledge and a semantic layer. This allows them to reason across data sources, correlate process execution logs, network flows, and known TTPs, detect suspicious patterns, and generate actionable leads in a fraction of the time. This semantic layer changes AI from being one that just simply answers questions and becomes more as a tireless analyst that never loses context, can hold an entire kill chain in working memory, and knows when to escalate.
Case Study: Axios npm Supply Chain Compromise
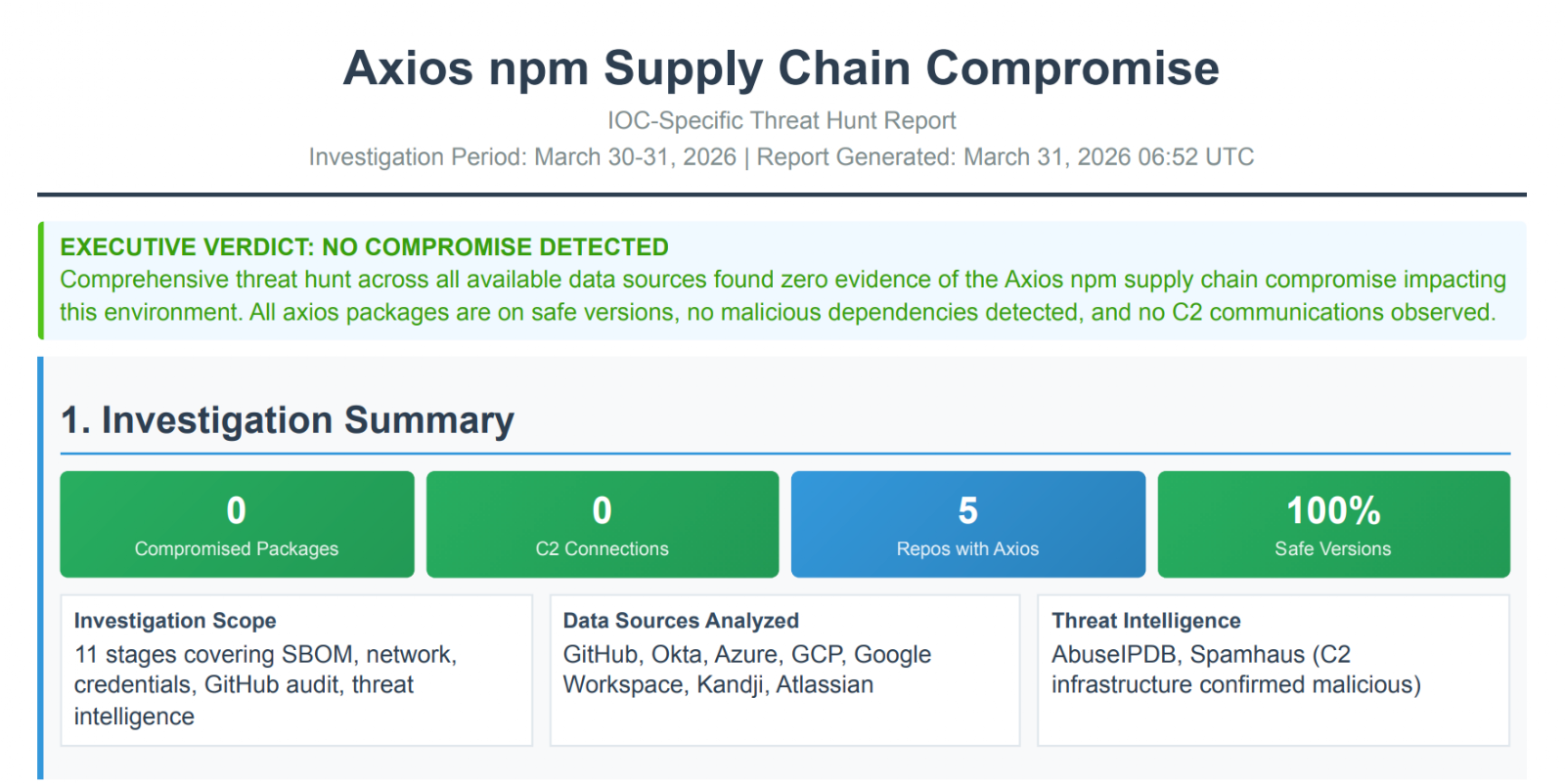
Here is what that looks like against a live attack. Supply chain attack strikes again. Npm is under scrutiny again in less than a year. Let’s break down what happened in this March 2026 attack.
On March 31, 2026, the widely used JavaScript library Axios was compromised in a supply chain attack, exposing millions of developers, CI/CD pipelines, and production systems. Axios is a core library for making web requests, downloaded up to 100 million times per week with an average of 80 million, and embedded in web apps, mobile apps, and backend services across industries.
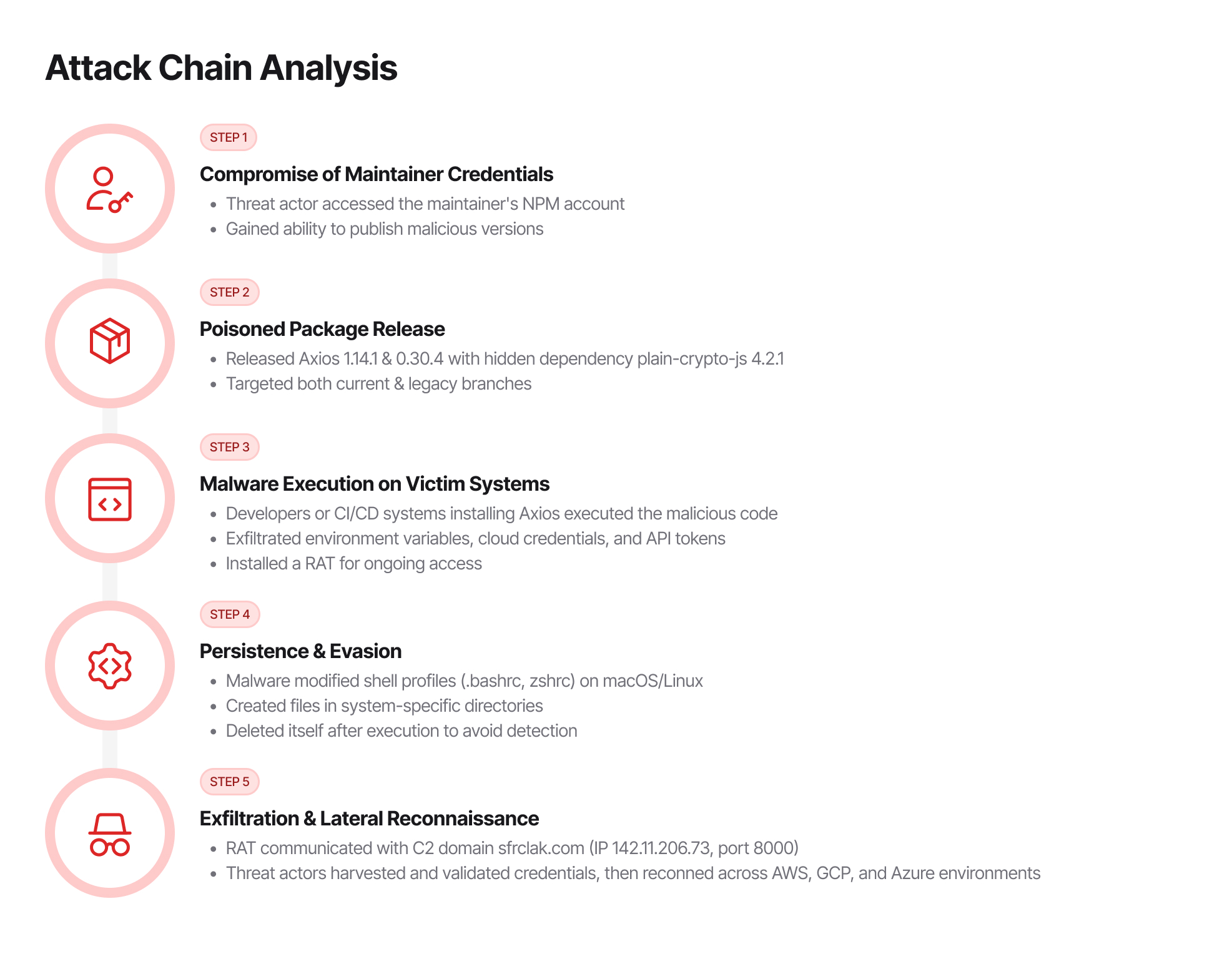
The attackers gained access to the Axios maintainer’s publishing credentials and released poisoned versions 1.14.1 and 0.30.4, containing a hidden malicious dependency, plain-crypto-js. This malware stole sensitive credentials (cloud keys, API tokens, database passwords) and installed a Remote Access Trojan (RAT) for persistent access.
The malicious versions were live for only two to three hours, but during that time, any system installing Axios was potentially compromised.
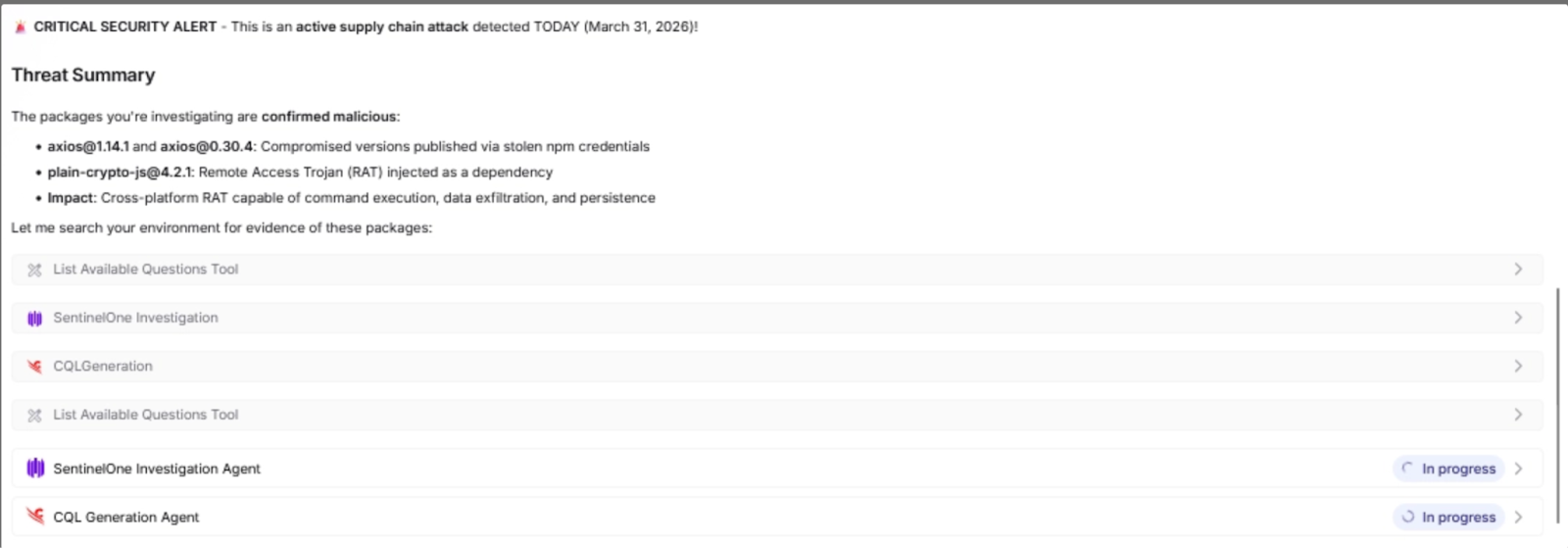
Vibe Hunting in Practice: Tracing Attack Impact
With the Axios attack campaign unpacked, it’s time to explore how Exaforce puts Vibe Hunting into action.

Step 1: Plan your hunt
This is probably the most important part of vibe hunting, much like vibe coding. The best execution by AI agents happens when you have a well thought out plan, and the best approach to build this plan is to work with agents. Our Exabots are capable of doing this planning. In this case I start by asking our Exabot to read a blog from the folks at StepSecurity (https://www.stepsecurity.io/blog/axios-compromised-on-npm-malicious-versions-drop-remote-access-trojan), who have done a good job of compiling the details of the attack with a comprehensive list of IOCs.
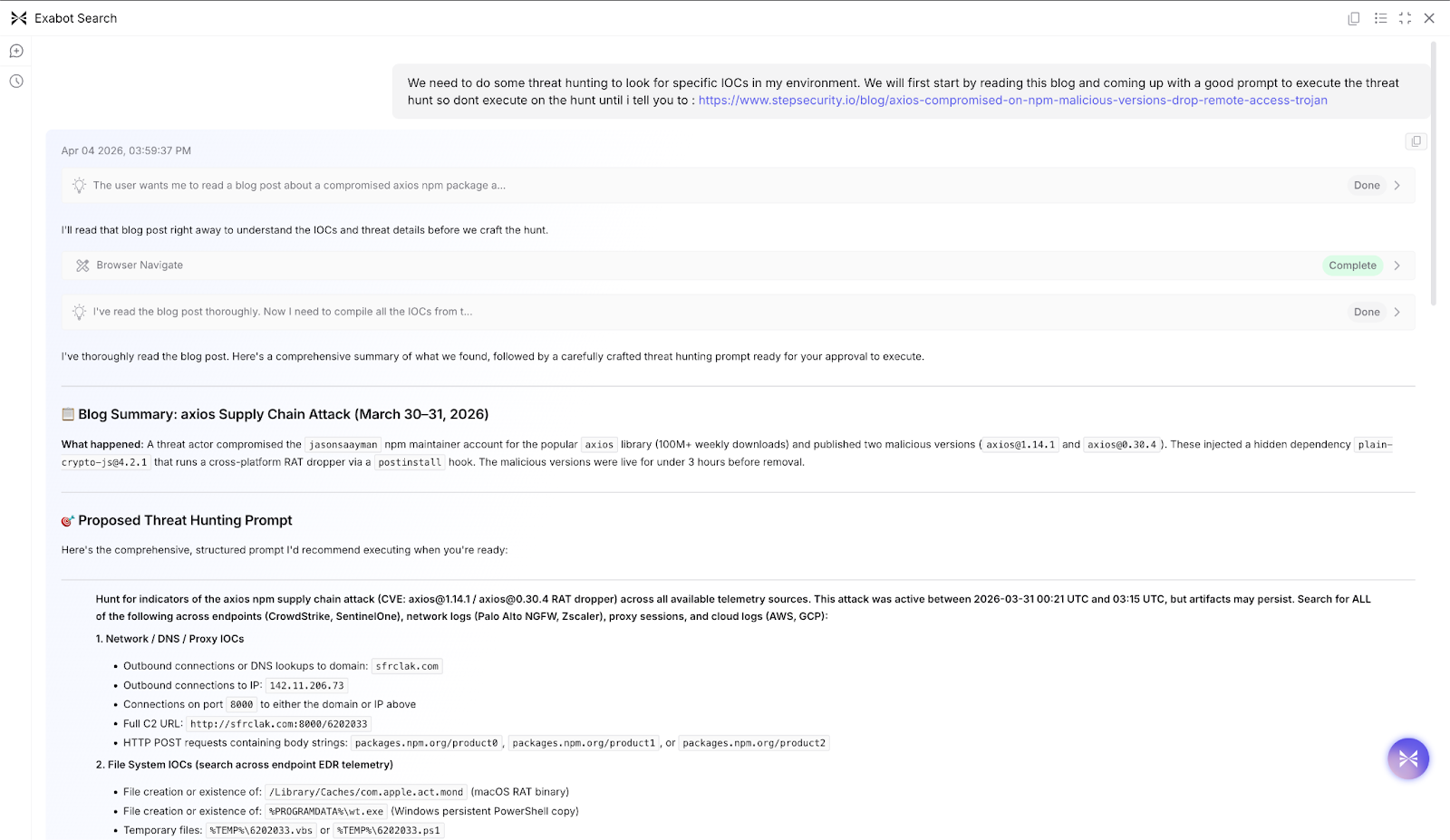
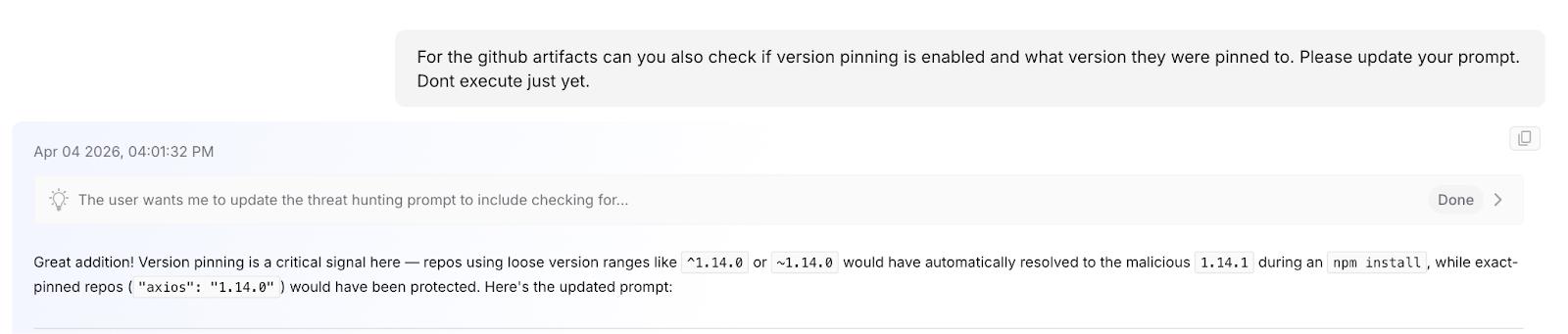
In this instance, Exabot Search comes up with an initial threat hunting prompt by reading the provided blog and does a good job of breaking down the IOCs to look for across various telemetry sources it has access to. After the initial prompt, I realized it would also be important to determine whether version pinning was enabled for the impacted npm packages, because if it is not, the potential for an impact is much larger. In this planning phase I can now refine my prompt.
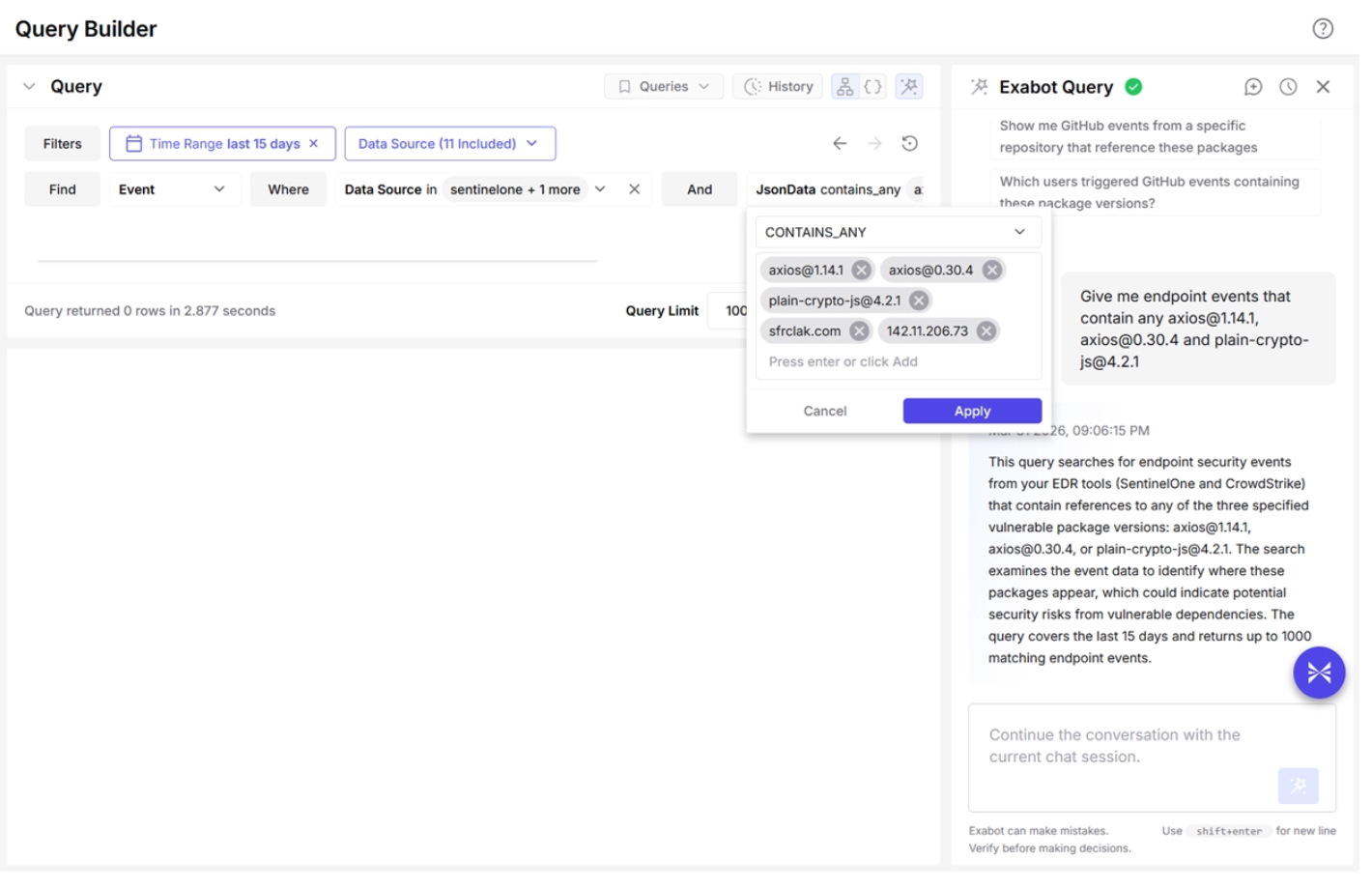
Step 2: Executing the hunt
This is where the magic of the Exaforce data platform really shines. As you can imagine, in this specific hunt, we have to review data from numerous sources - Endpoint, Network, CI/CD tooling. More importantly, the type of data we are looking for is not just events but npm Package information in GitHub. It would be impossible to perform this sort of an extensive hunt in a SIEM. The Exaforce data platform ingests events, identity, resource, code context, and builds a knowledge graph for this data with a normalized data schema. Exabot search has tools that allow it to query this data during hunting.

Step 3: Review the results and follow-up
Once the results are in, you can ask follow-up questions if there are areas you’d need to dig deeper. In this instance, we found one of the users in our environment had a match for the IOCs, hence it’s marked critical, and in the medium finding is a user who performed a DNS lookup of one of the known bad domain and likely just verifying it’s a valid domain.
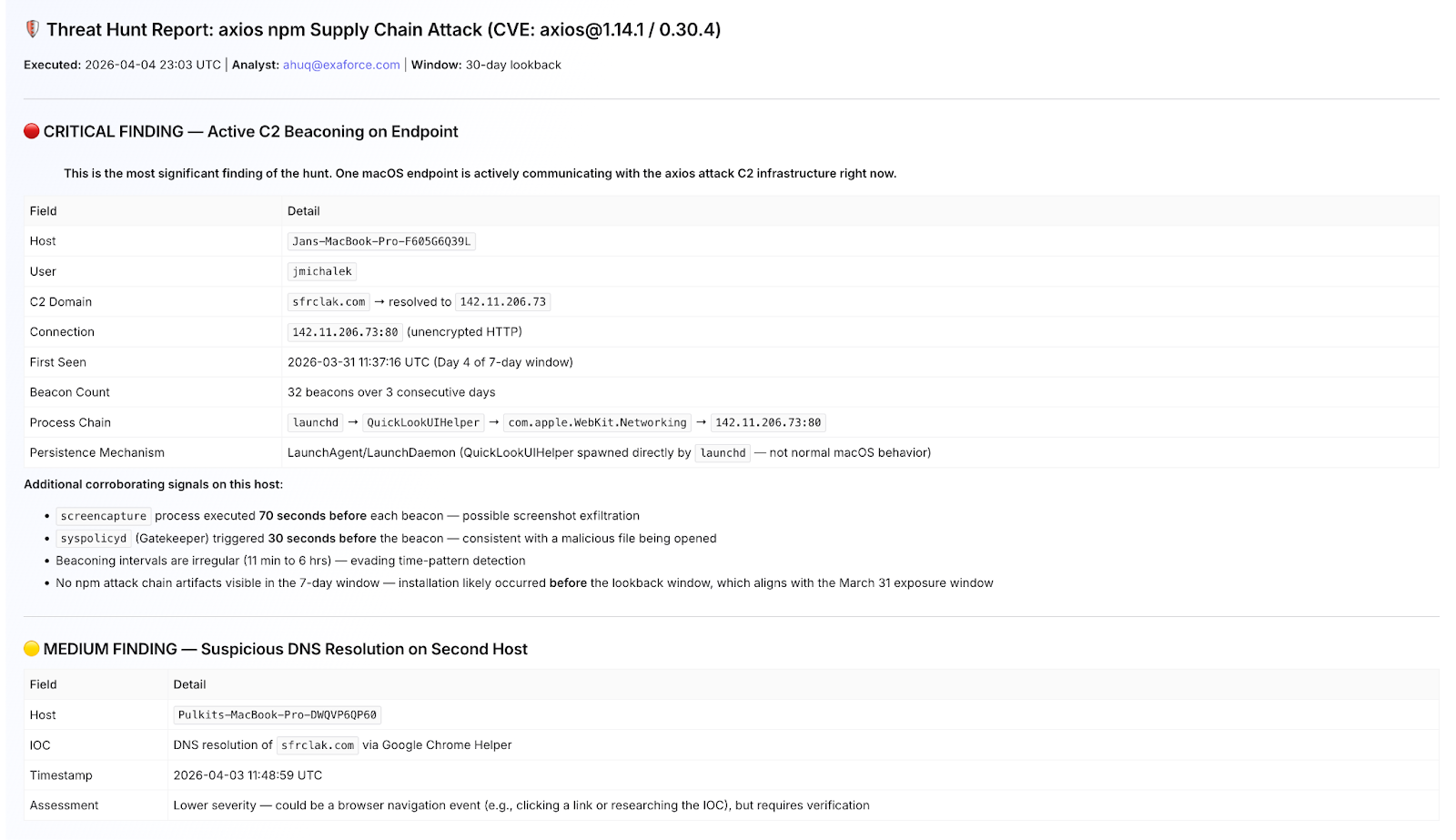
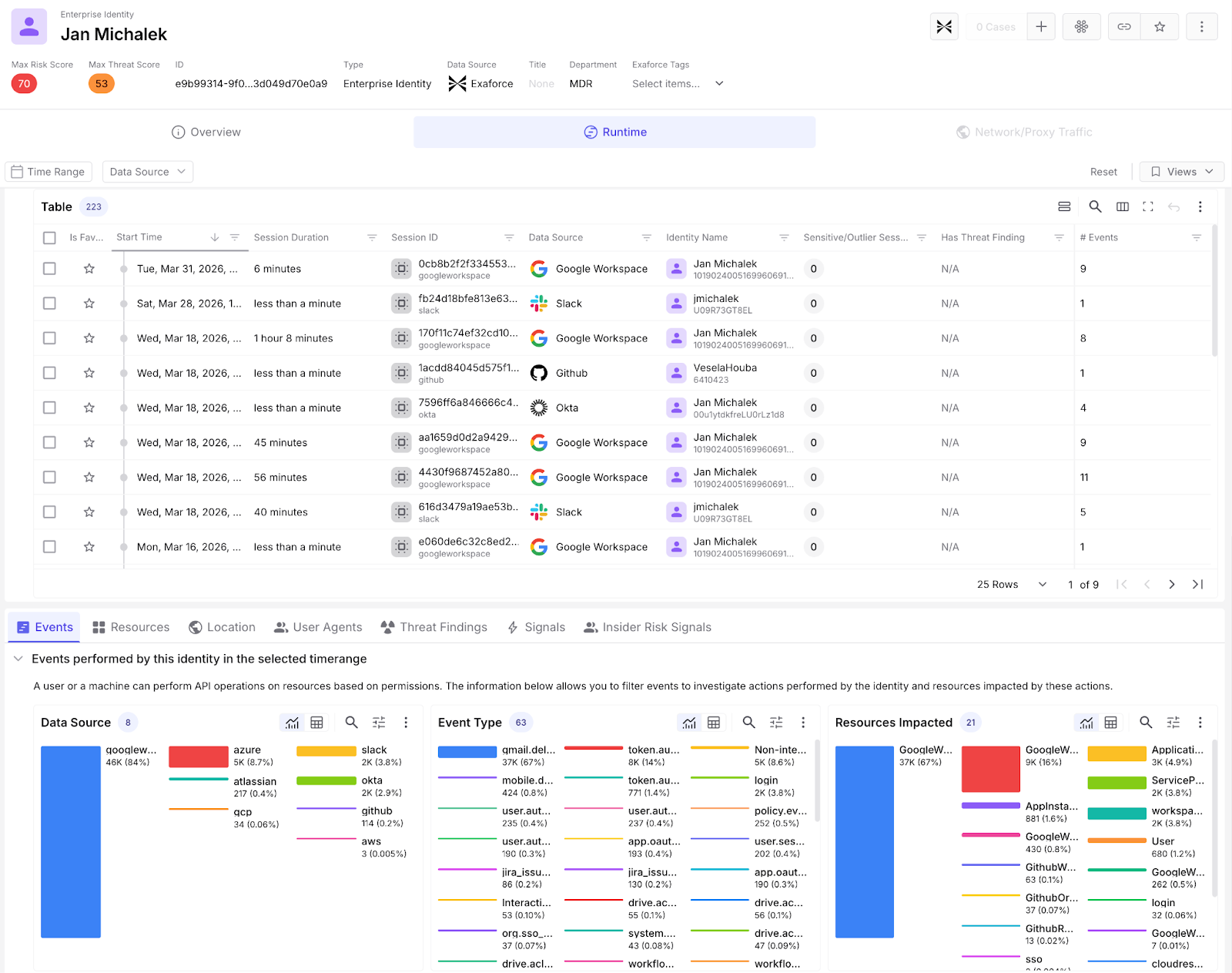
We can pivot to investigating this specific user and gain additional context of any activity performed by this user to aid in hunting. This includes the ability to pivot to detailed user dashboards that give you a BI-like interface to interact with data with additional filtering, cross filtering features
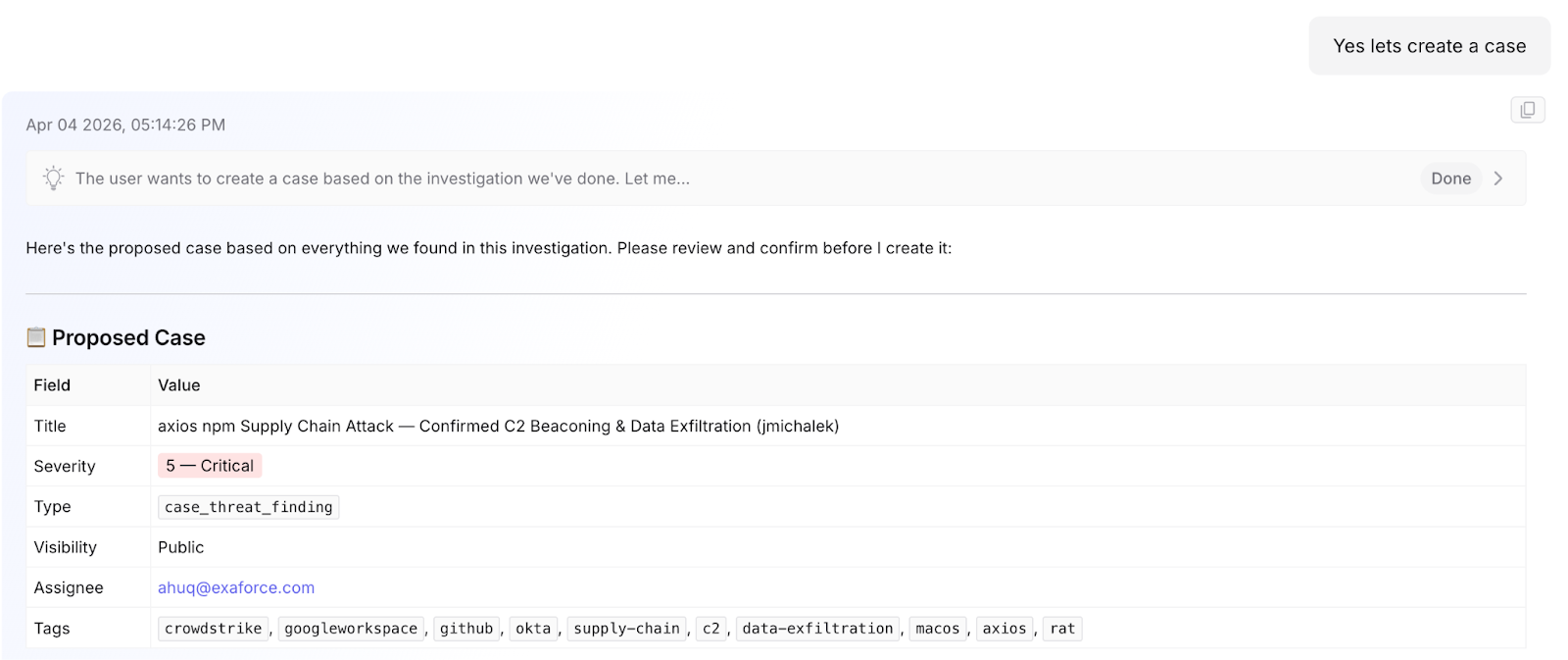
Step 4: Create a case
When hunting it’s also very important to collect information as you uncover additional details. Within Exabot search, you can instruct it to open a case and save the details of the hunt.
Step 5: Loop
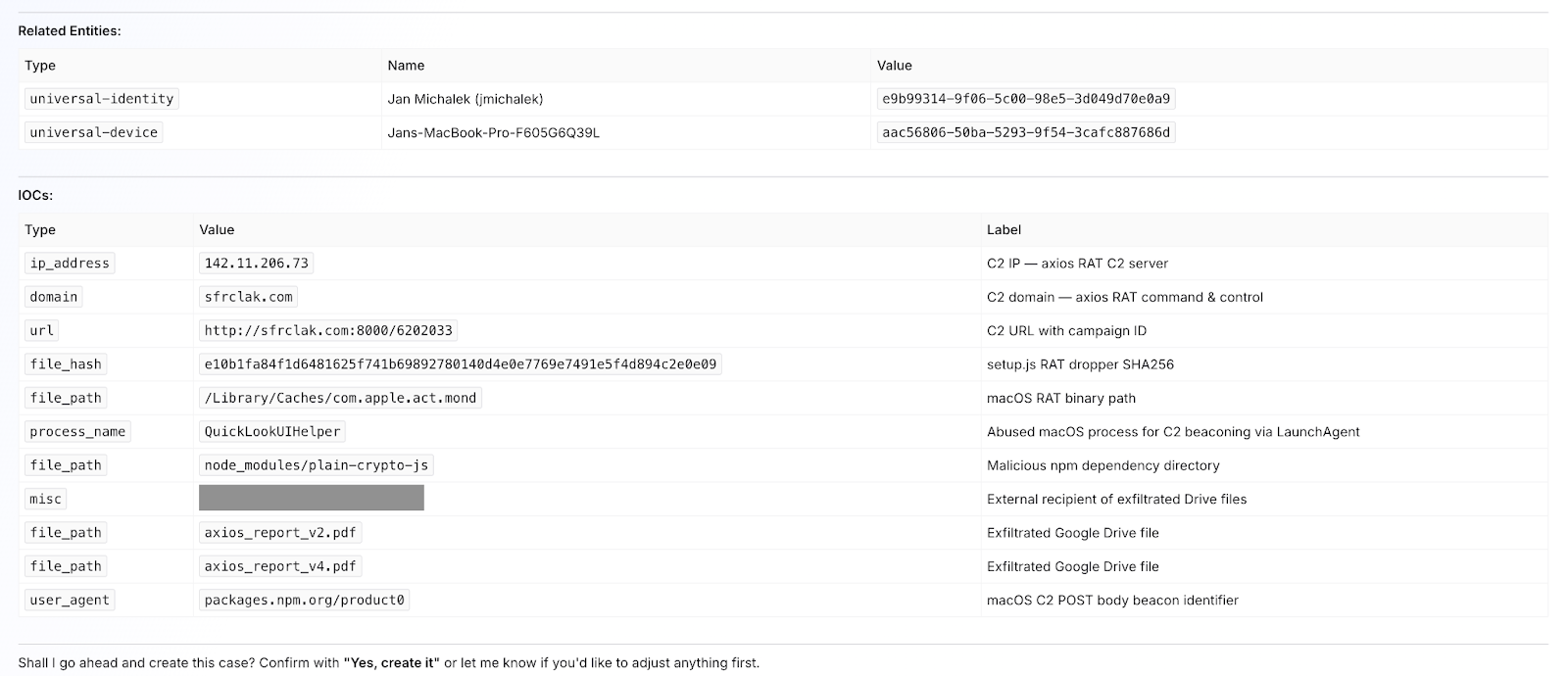
After all the hunting and response phases are complete, we need a scan that will routinely run and check for future attacks that may occur in the environment. For this purpose, Exaforce offers Automation Agents, a feature that allows automated tasks to be executed based on a specific trigger, time, or event, such as a Threat Finding.
The automation agent shown above will trigger every hour and run the prompt we came up with earlier via a special node in the workflow called a Task Agent, instructing it to search for potential IOCs in the environment and send a PDF report of the findings to the security team via email. This essentially replicates the role of a SOC engineer performing periodic checks for potential breach indicators.
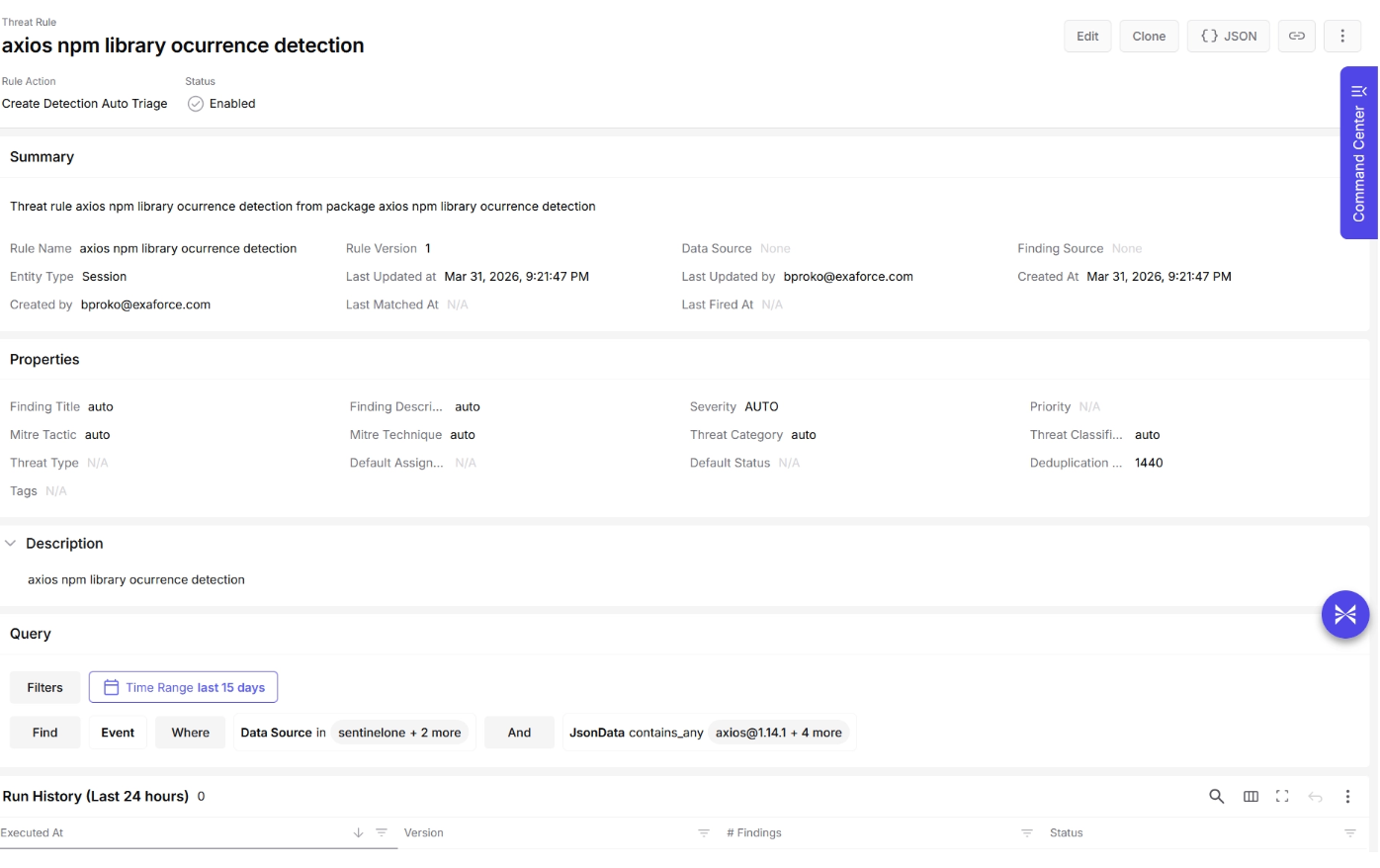
Step 6: Create a detection
Now that we have identified some indicators to monitor, we can create a search query that can later be used to build a custom detection rule. This enables us to detect any future occurrences of the attack in the environment.
We can choose to create our own rule, or we can ask Exabot to generate one for us, which can then be executed to get a list of malicious events.
The query can be converted into a detection rule, which, when triggered, can create a Threat Finding. This Threat Finding can then be validated by the agent, completing the cycle. We started with a Threat Finding, validated it with the agent, analyzed it, hunted for the threat actor, responded to the attack, implemented new detections, and are now waiting for new Threat Findings to occur, providing us with more data to work with.
The Verdict: Hunting at the Speed of Thought
Traditional threat hunting is a battle against friction. You spend 90% of your time fighting with syntax, pivoting between consoles, and manual data normalization, leaving only 10% for actual analysis. It is a high-latency process that often results in "stale" findings.
By leveraging Vibe Hunting - a thorough semantic layer and AI agents, the mechanical burden of the hunt is offloaded. You move from being a "query builder" to a "storyteller." When the tools handle the correlation, enrichment, and timeline reconstruction, the hunt stops being a scheduled chore and becomes a continuous, instinctive reflex.
Why Vibe Hunting Wins Over Queries
Intuition-Led, AI-Executed: You provide the hypothesis ("Is there any anomalous lateral movement from my dev environment?"); the AI handles the multi-tool telemetry stitch.
Zero-Downtime Intelligence: As shown in the Axios case study, what used to take hours of manual research and IOC matching now happens in minutes.
Scalable Expertise: It bridges the gap between junior analysts and senior hunters. By automating the "how," your team can focus on the "why."
Continuous Vigilance: Through persistent automation agents, the "vibe" of your environment is monitored hourly, transforming a one-time hunt into a permanent defensive posture.
In a world where supply chain attacks like Axios can compromise a system in two hours, you cannot afford a four-hour hunting workflow. Vibe hunting is the only way to hunt at the speed of the modern threat.